Bitmebx.com is a fake website posing as a cryptocurrency trading platform. Cybercriminals use this website to rob people of cryptocurrencies such as Bitcoin. This happens mainly through social media, where these criminals are active and try to entice people through fake accounts to deposit crypto in their deposits.
In this guide, I will explain how these criminals operate and how you can avoid becoming the next victim in the future. This is not always completely preventable, but by reading the information in this article, you will become better informed and recognize this type of scam next time.
How does the Bitmebx.com scam work?
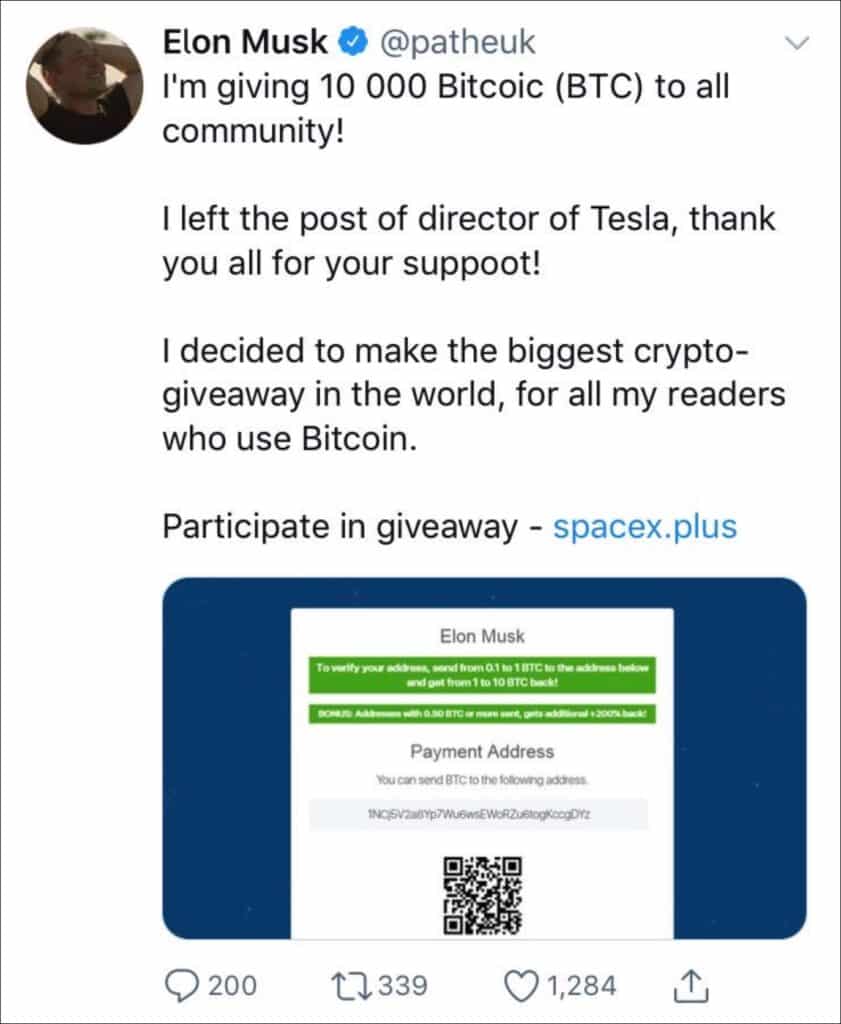
Social media and famous people
As I mentioned earlier, this scam works mainly through social media. Criminals abuse famous people on social media to lure customers to their scams. This is done with promo codes and promo videos in which famous people, such as Elon Musk, Bill Gates, Drake, etc., talk about why they joined this Bitmebx.com crypto website. However, the videos are fake. They are made with Artificial intelligence. Often, the famous person is fake, and an AI voice has been put behind them, making it seem like these individuals are participating in this scam.

Discount Codes (Promo Codes)
Through this type of fake video, customers are lured with discount codes and images that appear to show cryptocurrencies being traded. The ultimate goal is to lure people to the Bitmebx.com website.
Bitcoin deposit
Once on this website, the victim is asked to enter a promo code or voucher. Once this is done, the victim’s statement supposedly credits 0.31 BTC. This is not the case, but it appears that way.
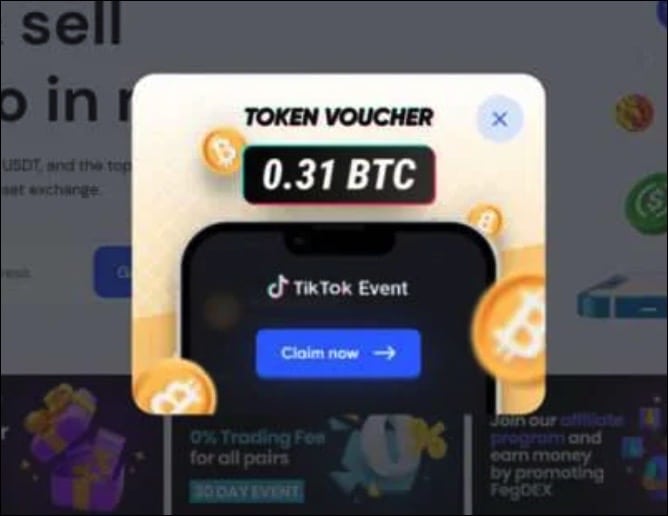
After this, the scam is initiated. First, the customer is asked to deposit BTC to withdraw the bitcoins. When the customer does this, suddenly, there is no BTC available. The Bitmebx.com website is closed, and the scammers make off with the customer’s Bitcoin.
What can I do if I am a victim of Bitmebx.com?
Disconnect all contact
The first thing you should do is sever all contact with Bitmebx.com. Do not contact them anymore, do not respond to invitations, and do not send Bitcoin to get your money back.
Change your passwords
After you break contact, you should change all your passwords. Did you use a password to log into this fake Bitmebx.com website? Then, make sure you change all your passwords that may match this password.
Contact your bank or exchange
Contact your financial institution immediately if you transferred money from your bank or used a credit card. They may have fraud protection mechanisms that can help. Also, keep an eye on your credit card debts at all times. If you have used your credit card, stop all unknown transactions. You do not want money to be stolen again by this criminal gang.
Report Bitmebx.com to financial fraud authorities
Different countries have specific regulatory bodies for financial fraud and cybercrime. In the US, you can report to the Federal Trade Commission (FTC) through its website. If Bitmebx.com involves investment fraud, It should be reported to the Internet Crime Complaint Center (IC3) and the Securities and Exchange Commission (SEC).
Contact a fraud professional
Have you lost a lot of money? If so, contact a professional who specializes in fraud cases. It can also help contact cryptocurrency exchanges by informing them they can prevent this scam.
How to avoid becoming a victim of crypto fraud
It is not always easy to avoid becoming a victim of crypto fraud, for example, yet there are some things to watch out for.
Stay informed about crypto trading
Make sure you are aware of how crypto trading works. By learning how crypto coins are traded and the technology behind them works, you can spot some of the fraudsters.
Is the offer too good to be true?
As with other scams, does the offer seem too good to be true? Then, reject it or do thorough, independent research. Don’t be persuaded to get rich quickly, don’t accept an offer from someone who supposedly cares about you, always ask questions, and ask for additional proof.
Do research on the internet
Do thorough research on the Internet. Make sure you look up the name of the company that deals in cryptocurrencies, check out reviews from other customers or reputable websites, and do not engage in crypto trading through social media. For example, by doing proper research on Bitmebx.com, you could have known that this website is a scam.
Do research on the owner and team
Is someone posing to trade in cryptocurrencies? Then, look up this person’s name, company, and employees online. If you can’t find anything about this person or find bad experiences from other customers, you might be dealing with a scam. So, do some thorough research into the people behind the website Bitmebx.com. You may be able to recognize scams right away.
Discuss the offer with family members
Sometimes, tips from others can change the way you view Bitmebx.com. So, are you going to trade in cryptocurrencies, or are you about to transfer a large amount of money in Bitcoin but just don’t feel like everything is right yet? Then, get in touch with family members or friends and let them review what their views are on this company.
Uninstall unwanted programs
In this phase, we’ll ensure your computer is free from adware. Often, adware sneaks onto your system because it’s packaged with free software downloaded from the web.
During installation, adware presents itself as a beneficial tool or bonus feature. You might inadvertently install adware if you rush through the setup without reading each step. This deceptive practice can be avoided by employing tools like Unchecky. Follow the instructions below to detect and eliminate any adware on your system.
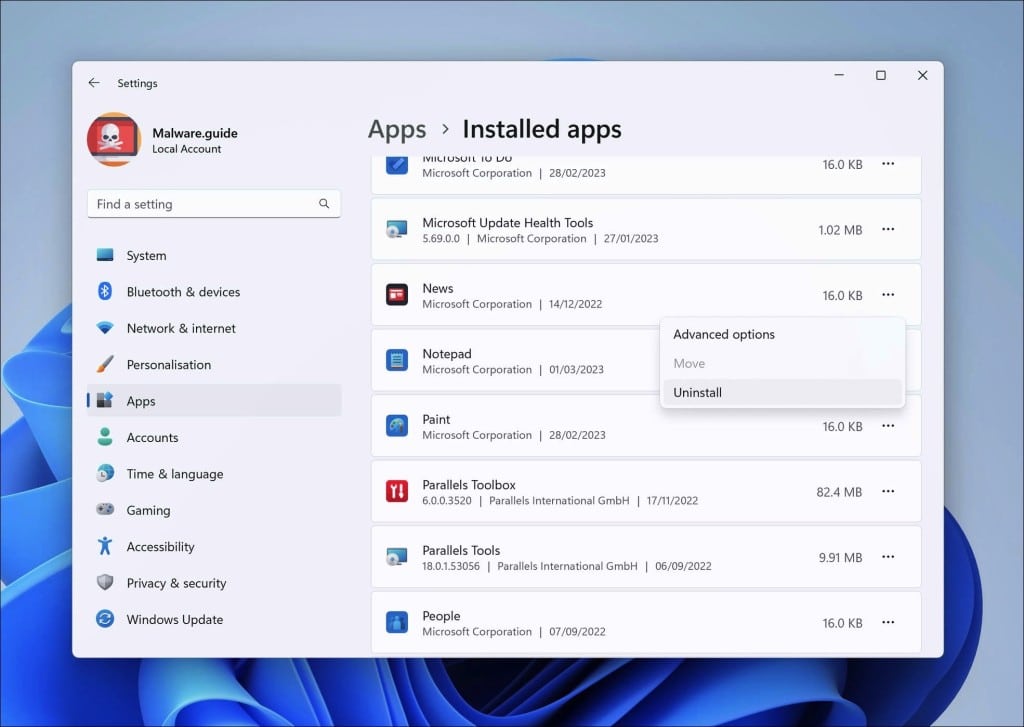
Windows 11
- Click on “Start.”
- Click on “Settings.”
- Click on “Apps.”
- Lastly, click on “Installed apps.”
- Search for any unknown or unused software in the list of recently installed apps.
- On the right-click on the three dots.
- In the menu, click on “Uninstall.”
→ See the next step: Malwarebytes.
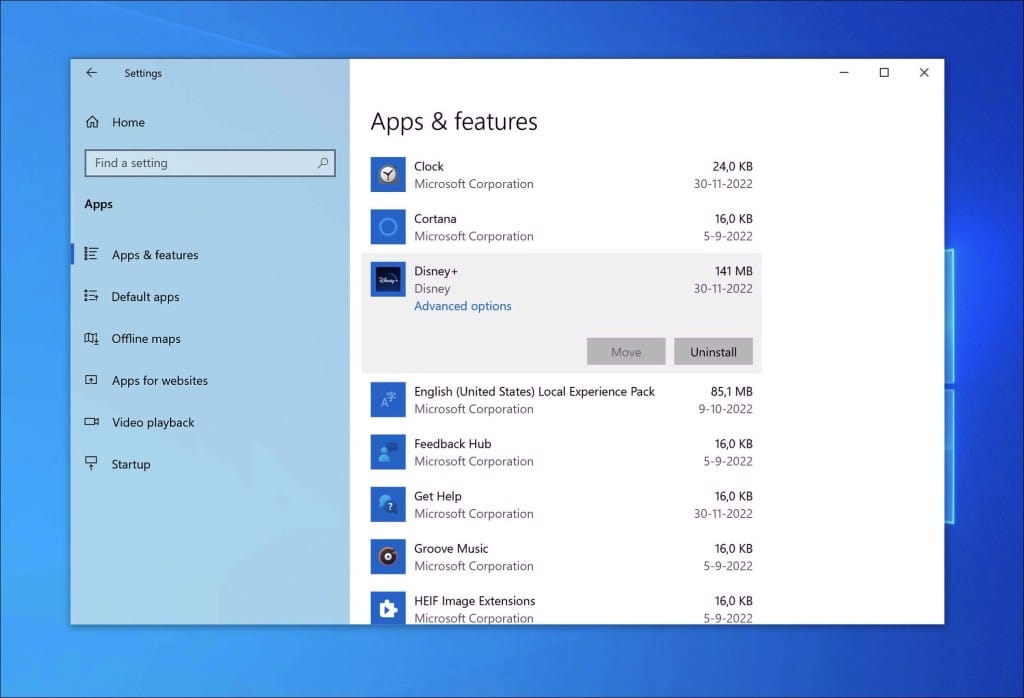
Windows 10
- Click on “Start.”
- Click on “Settings.”
- Click on “Apps.”
- In the list of apps, search for any unknown or unused software.
- Click on the app.
- Lastly, click on the “Uninstall” button.
→ See the next step: Malwarebytes.
8. Scan your computer for malware
Alright, let’s get down to brass tacks! You’ve tidied up by uninstalling those pesky adware apps that promote the Bitmebx.com crypto scam, but let’s do one more sweep to ensure everything’s in tip-top shape.
Malwarebytes
Listen, manually hunting down malware is like trying to find a needle in a haystack. It’s tricky and time-consuming, and if you’re not a tech guru, there’s a good chance you might miss something—or worse, accidentally mess something up. This is like DIY electrical work; you don’t want to risk it.
Malwarebytes. Think of it as a digital detective for your computer. It’ll comb through your system, searching for villains like Bitmebx.com scams and other unwanted guests. The beauty of Malwarebytes? Scanning and cleaning your computer of malware doesn’t cost a dime. And if you fancy a bit more protection, it’s covered, too.
Even if you think your computer is clean, give Malwarebytes a spin. It’s always better to double-check. Peace of mind is priceless, after all!
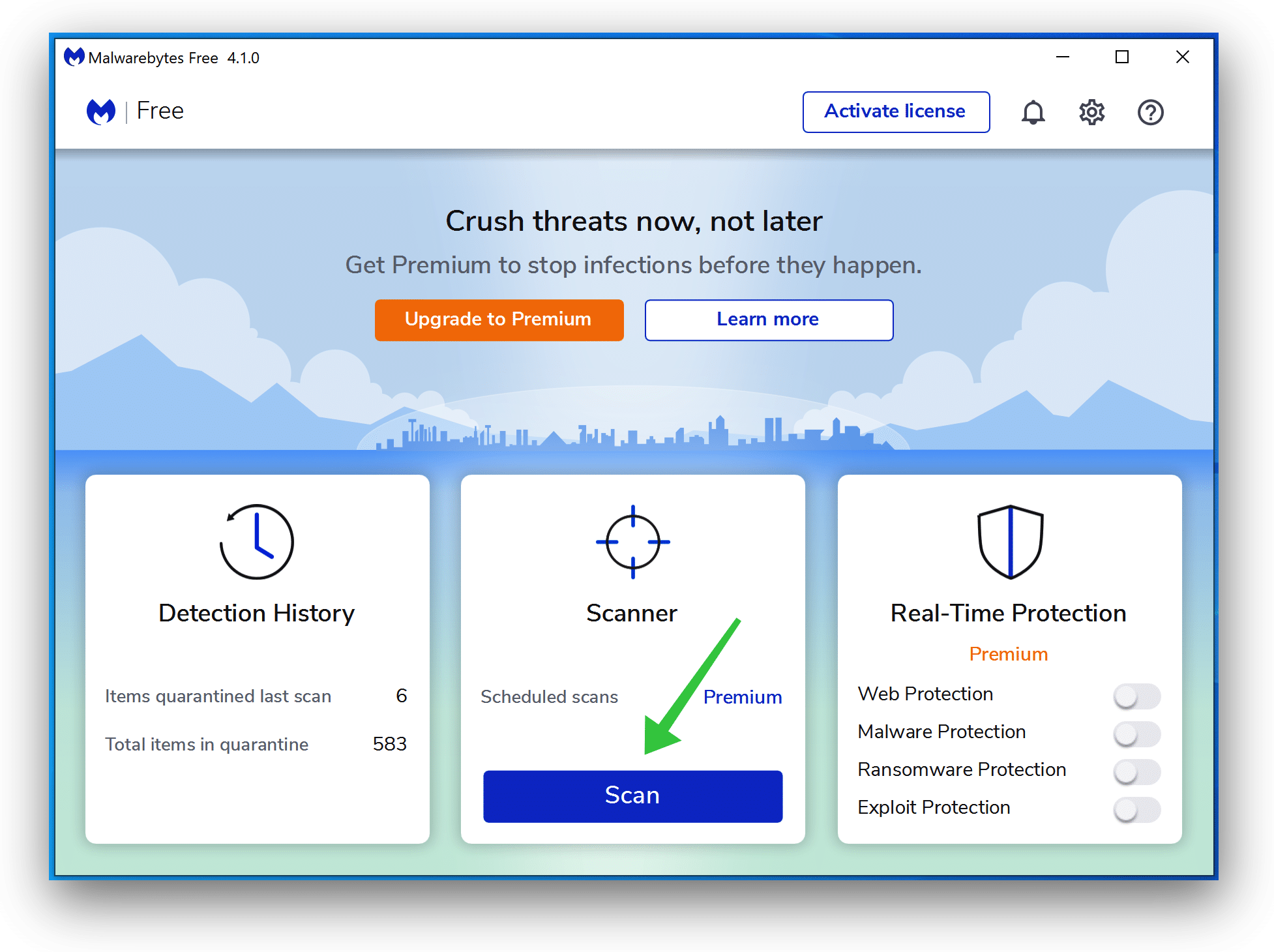
- Download Malwarebytes
- Install Malwarebytes, and follow the on-screen instructions.
- Click Scan to initiate a malware scan on your PC.
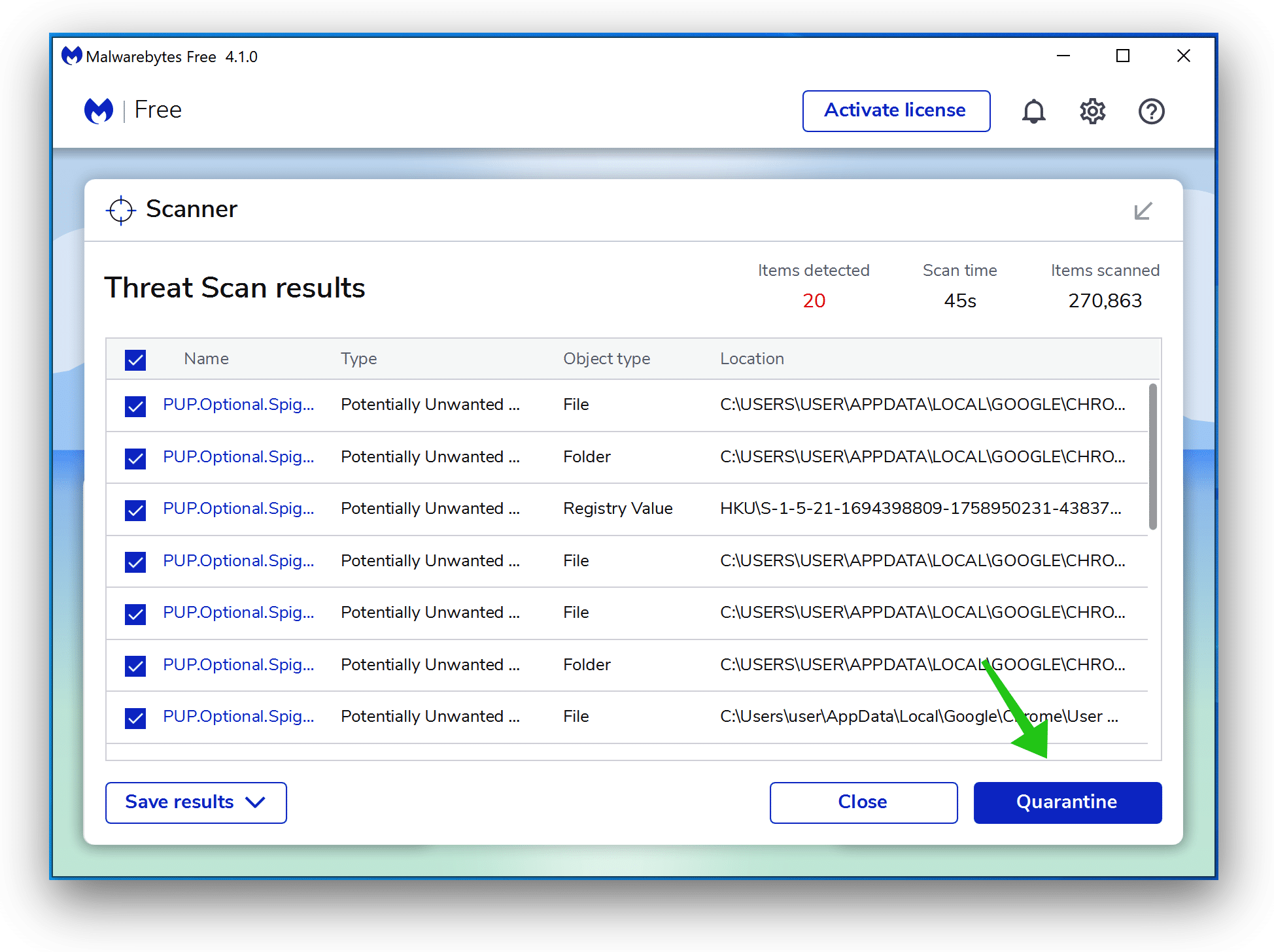
- Wait for the Malwarebytes scan to finish.
- Once completed, review the malware detections.
- Click Quarantine to continue.
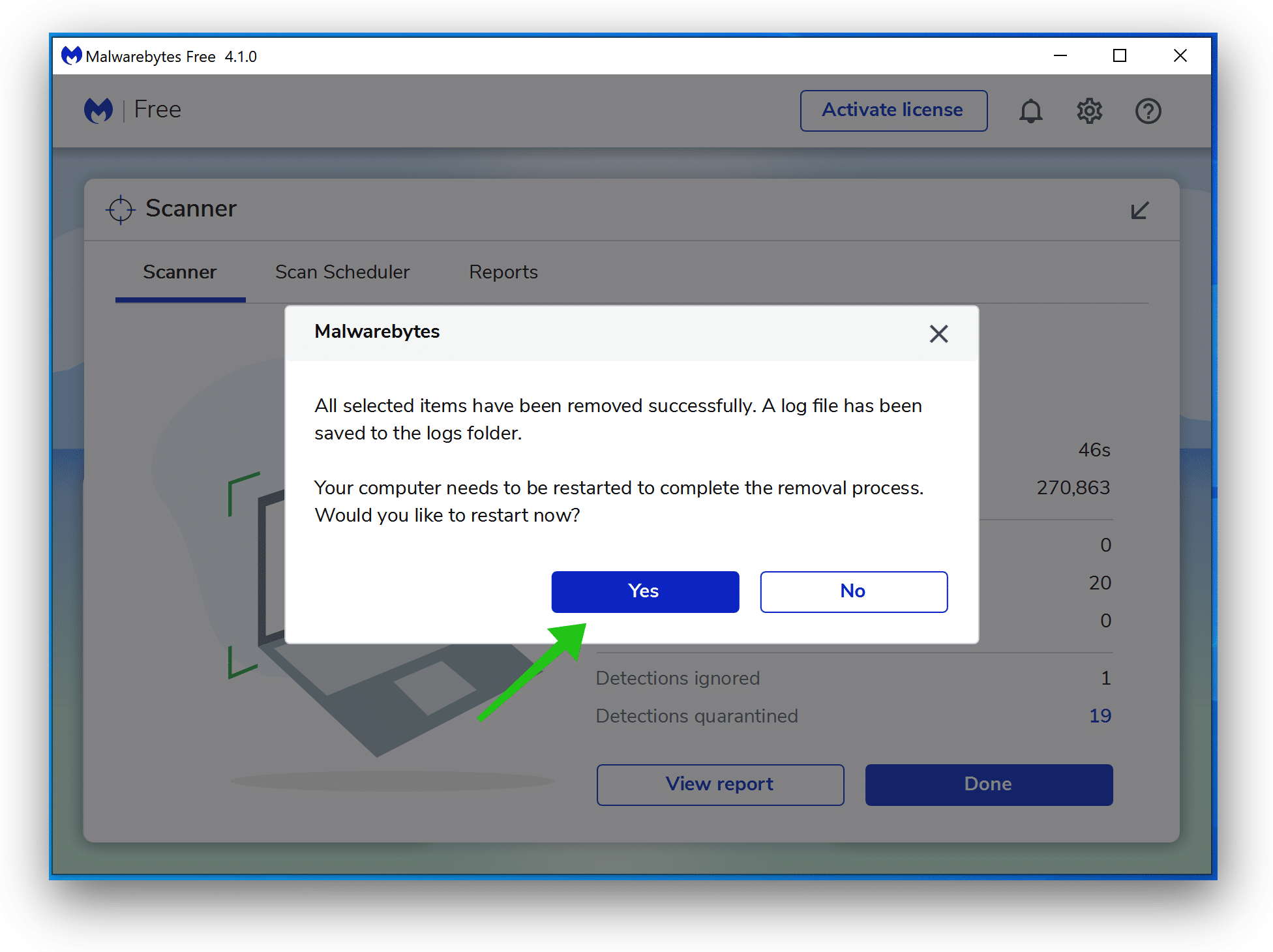
- Reboot Windows after all the malware detections are moved to quarantine.
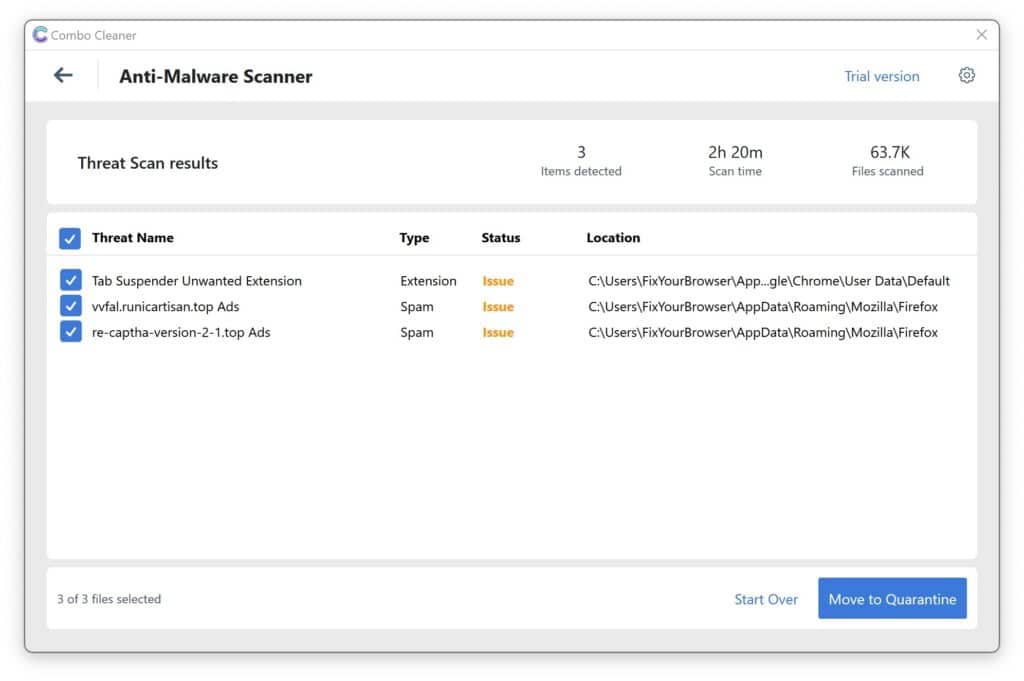
Combo Cleaner
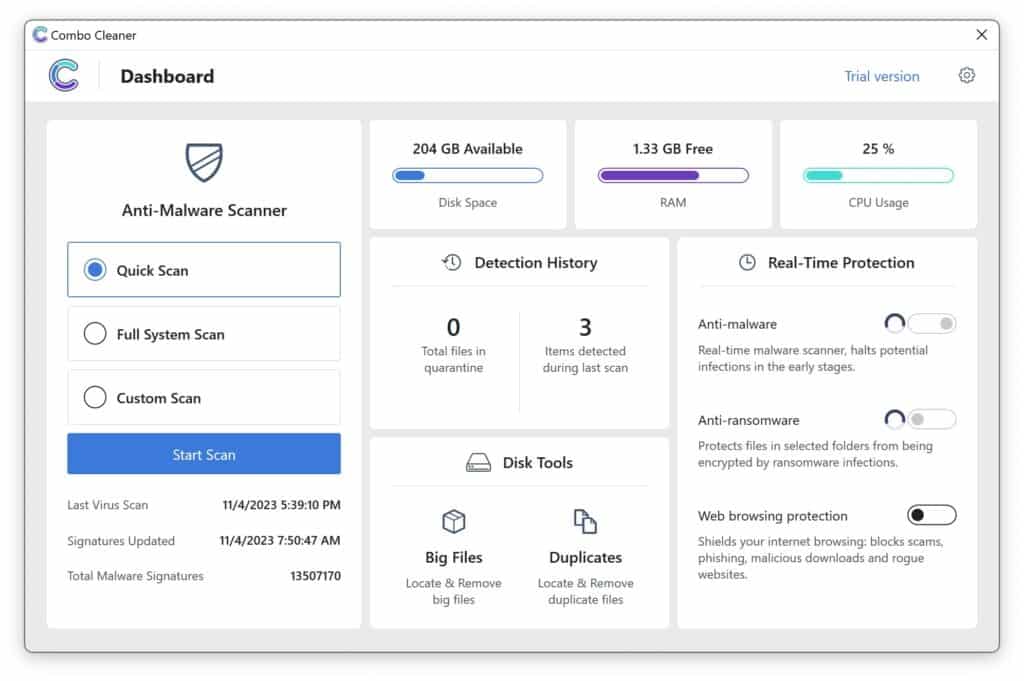
Combo Cleaner is a cleaning and antivirus program for Mac, PC, and Android devices. It is equipped with features to protect devices from various types of malware, including spyware, trojans, ransomware, and adware. The software includes tools for on-demand scans to remove and prevent malware, adware, and ransomware infections. It also offers features like a disk cleaner, big files finder (free), duplicate files finder (free), privacy scanner, and application uninstaller.
Follow the installation instructions to install the application on your device. Open Combo Cleaner after installation.
- Click the "Start scan" button to initiate a malware removal scan.
- Wait for Combo Cleaner to detect malware threats on your computer.
- When the Scan is finished, Combo Cleaner will show the found malware.
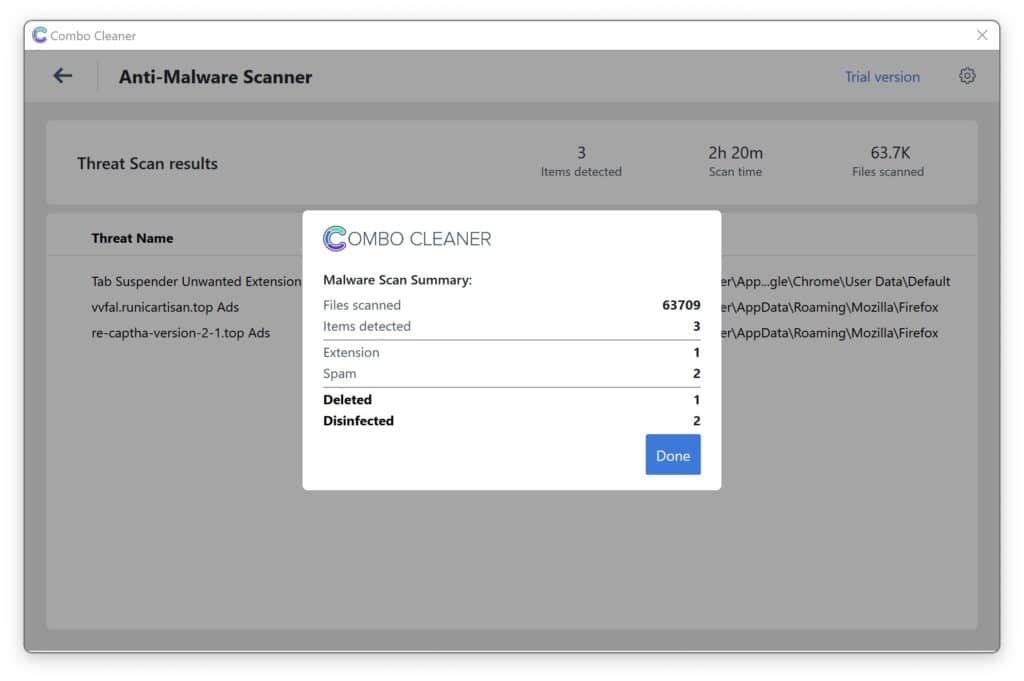
- Click "Move to Quarantine" to move the found malware to quarantine, where it can't harm your computer anymore.
- A malware scan summary is shown to inform you about all threats found.
- Click "Done" to close the scan.
Use Combo Cleaner regularly to keep your device clean and protected. Combo Cleaner will remain active on your computer to protect your computer from future threats that try to attack your computer. If you have any questions or issues, Combo Cleaner offers a dedicated support team available 24/7.
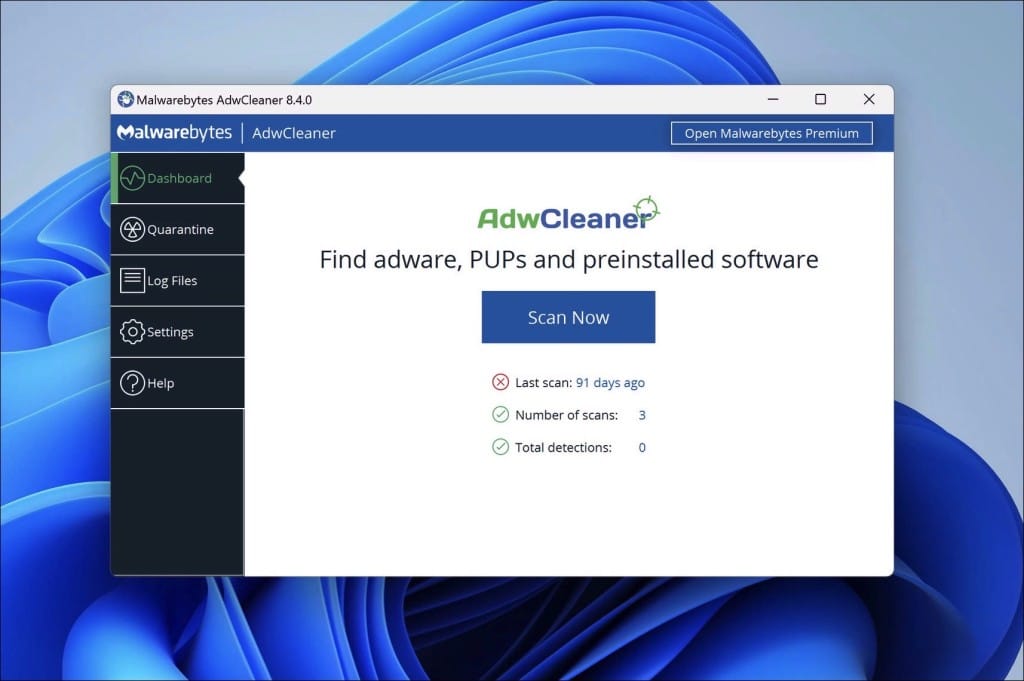
AdwCleaner
I have the perfect tool if you’ve been bothered by pesky pop-ups or strange browser behaviors. It’s called AdwCleaner. The good folks at Malwarebytes created this handy, free tool to help folks like us tackle annoying adware, those unwanted programs that sneak into our computers, and even browser hijackers like Bitmebx.com.
Think of AdwCleaner as a detective that scans your computer. It’s looking for programs and toolbars you never asked for or those that make your computer sluggish or your browser laugh. And the best part? You don’t need to be a tech whiz to use it.
When AdwCleaner finds these nuisances, it safely kicks them out. If your browser’s been acting up because of some unwanted software or things don’t look as they used to, AdwCleaner can also reset it, bringing things back to how they should be.
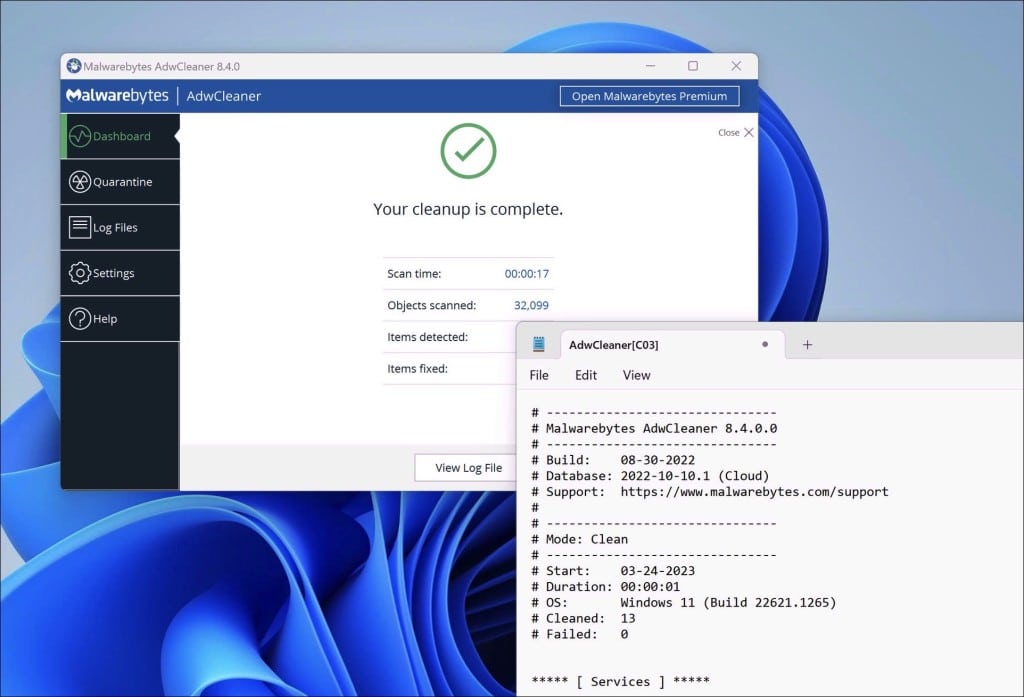
- Download AdwCleaner
- No need to install AdwCleaner. You can run the file.
- Click “Scan now.” to initiate a scan.
- AdwCleaner starts downloading detection updates.
- Following is a detection scan.
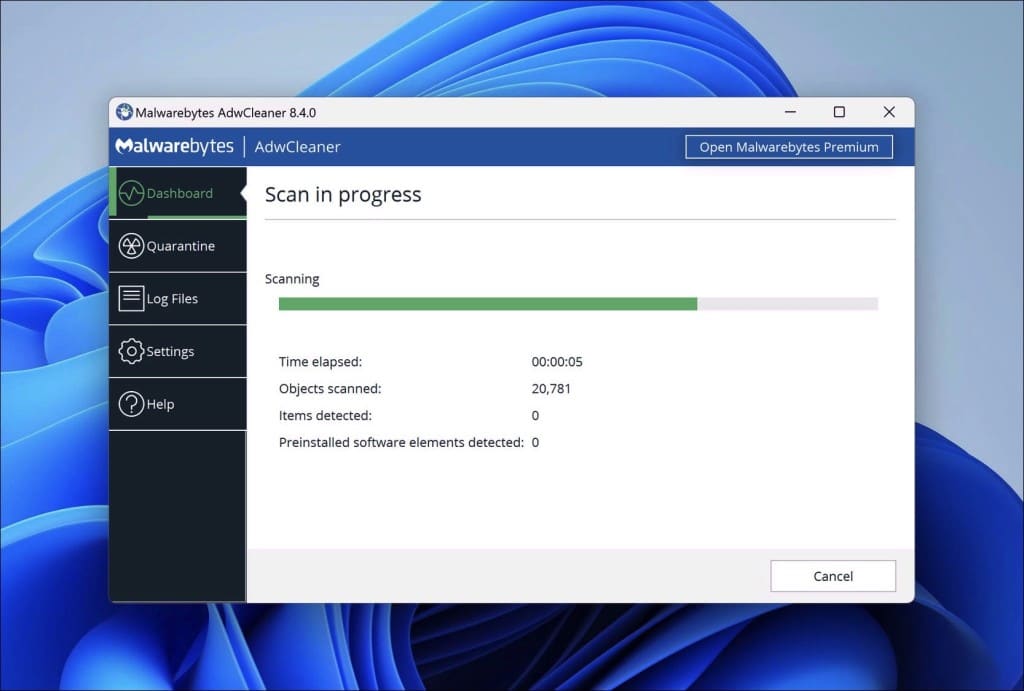
- Once the detection is finished, click on “Run Basic Repair.”
- Confirm by clicking on “Continue.”
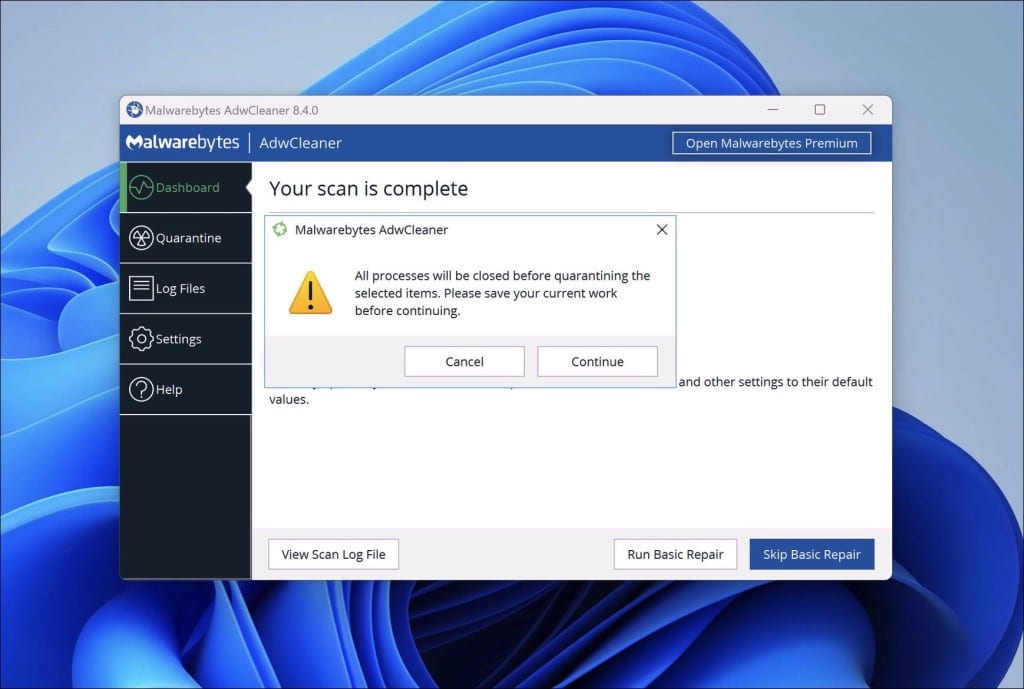
- Wait for the cleanup to complete; this won’t take long.
- When Adwcleaner is finished, click “View log file.” to review detections and cleanup processes.
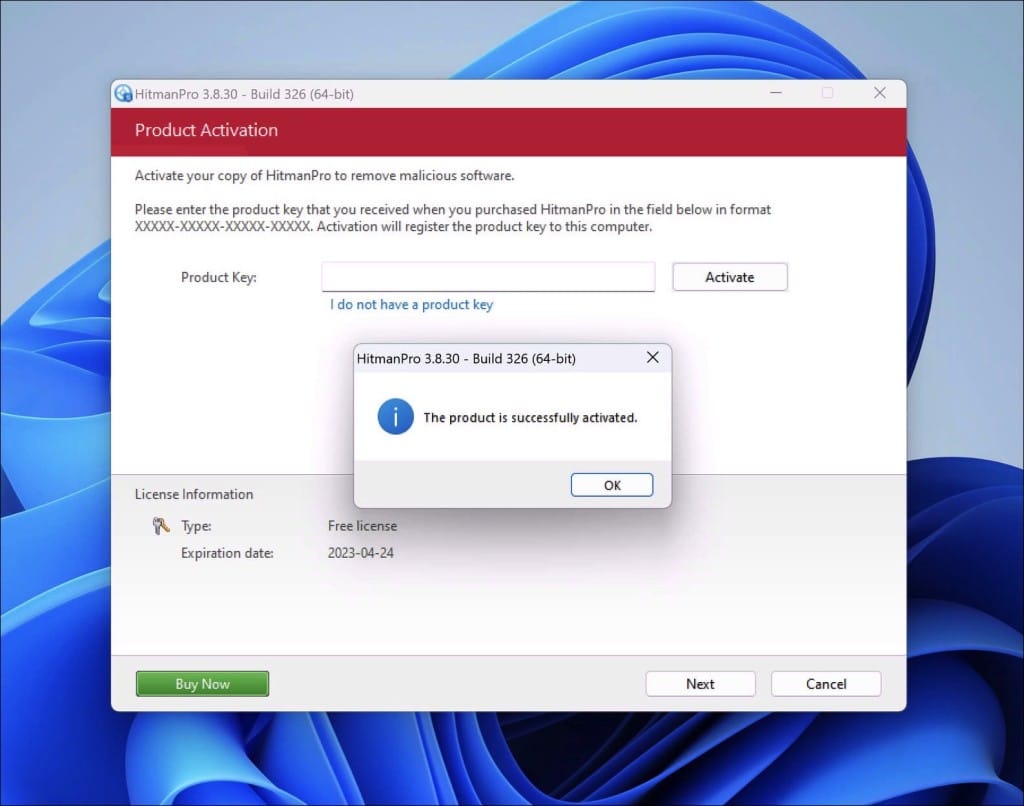
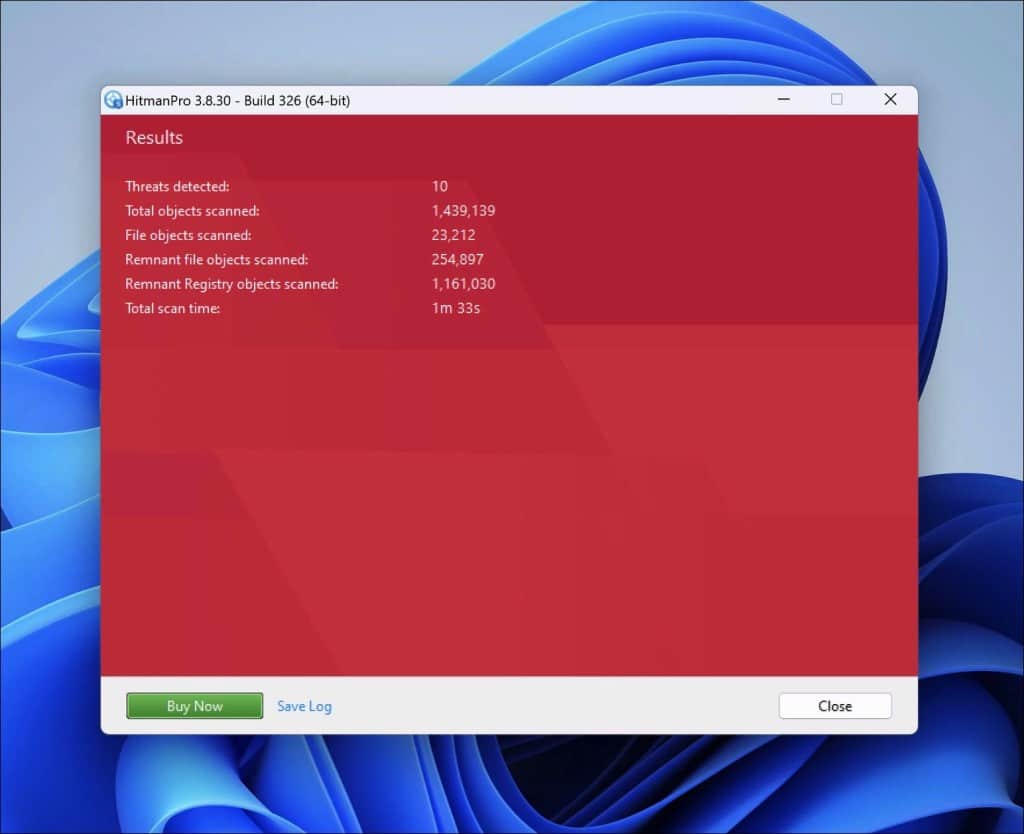
Sophos HitmanPRO
Ever heard of HitmanPro? Imagine it as a super-sleuth that doesn’t just look for clues on the crime scene (your computer) and sends evidence to a high-tech lab (Sophos cloud) for further analysis. Neat, right?
Unlike the traditional gumshoe detectives (standard anti-malware tools) that rely solely on their toolkit, HitmanPro gets an extra set of eyes from the cloud. By sending samples up there, it can detect sneaky malware faster and with laser precision.
Stumbled upon those pesky Bitmebx.com scam pop-ups? No worries. HitmanPro’s got your back. It will hunt down the sneaky culprit causing that pop-up and kick it out. And if you decide to keep HitmanPro as your digital bodyguard, it’ll ensure you’re shielded from all sorts of online nasties in the future. So, for a faster, cloud-boosted malware detective, give HitmanPro a spin!
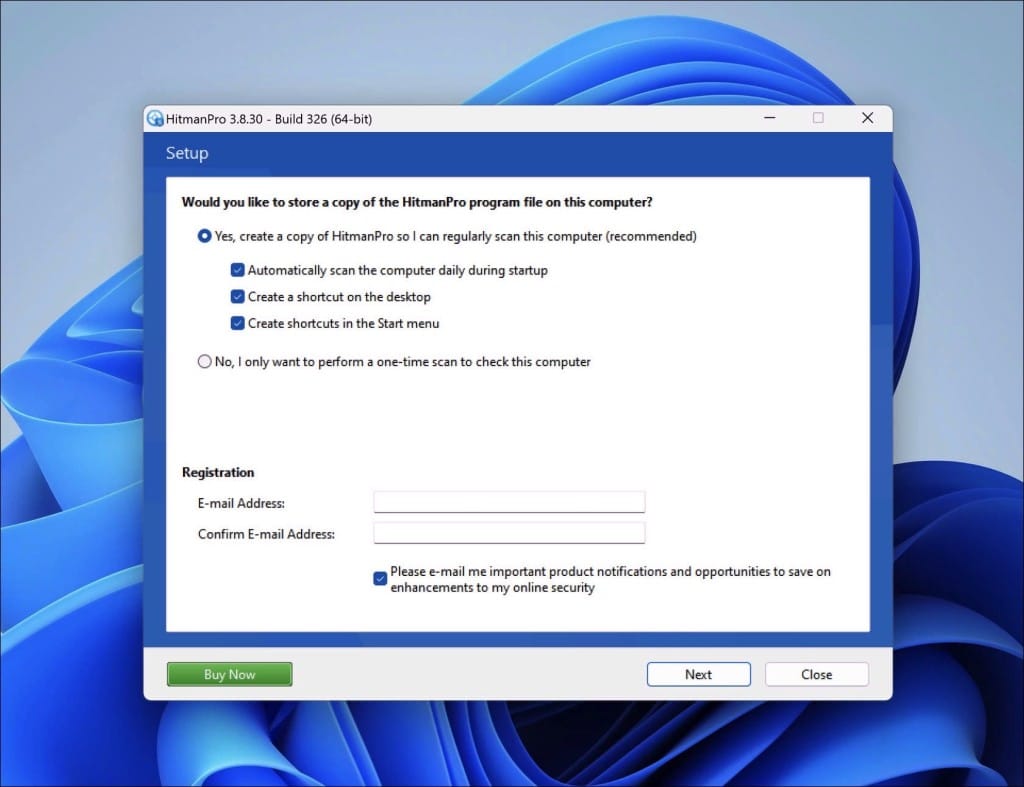
- Download HitmanPro.
- Click the “Next” button to continue the setup.
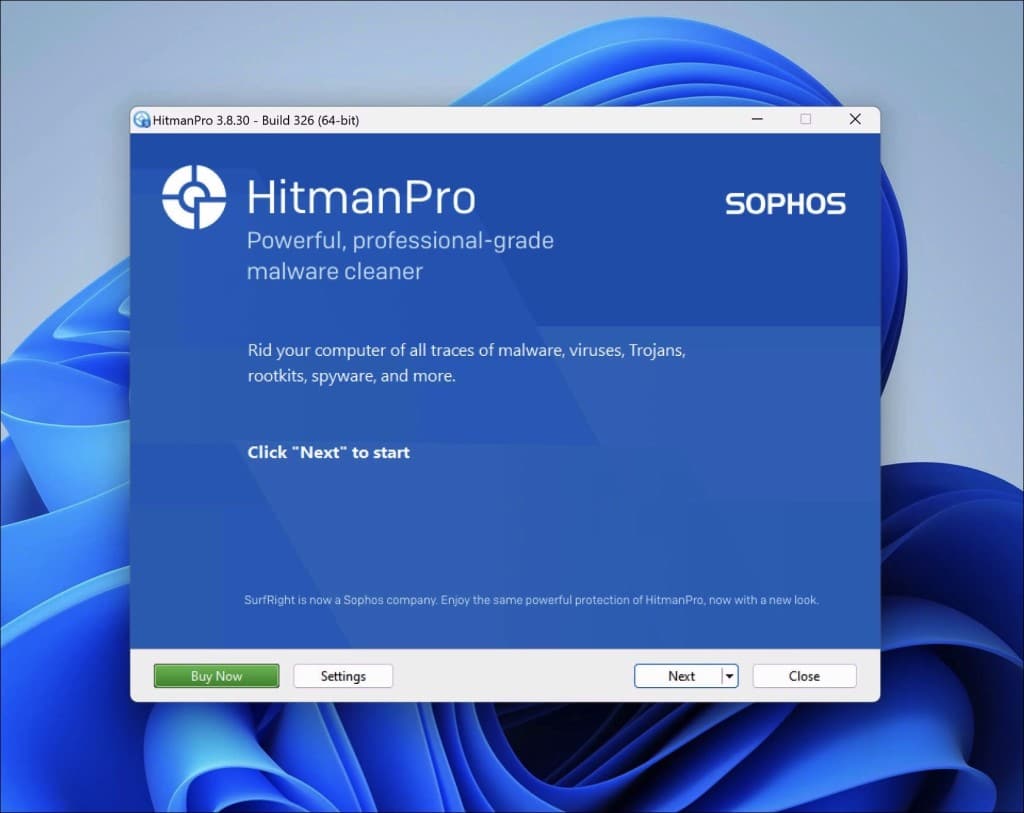
- Accept the terms and conditions to use Sophos HitmanPro.
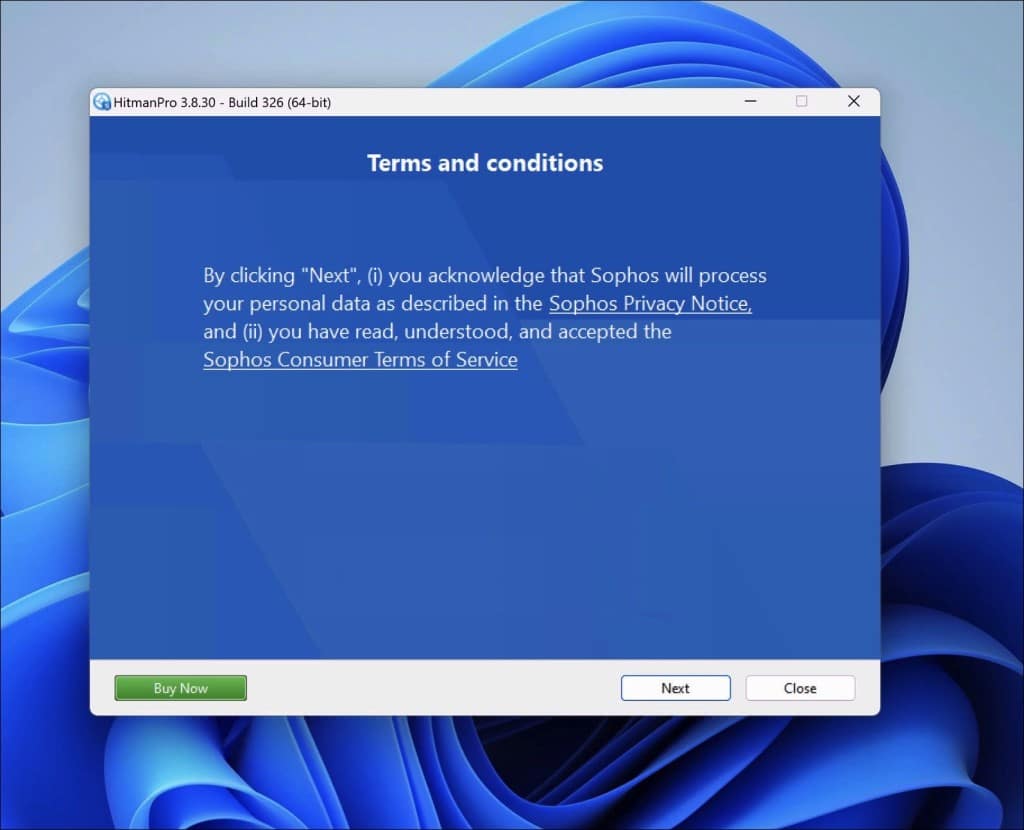
- If you want to scan your computer regularly, click “yes.” If you do not want to scan your computer more often, click “No.”
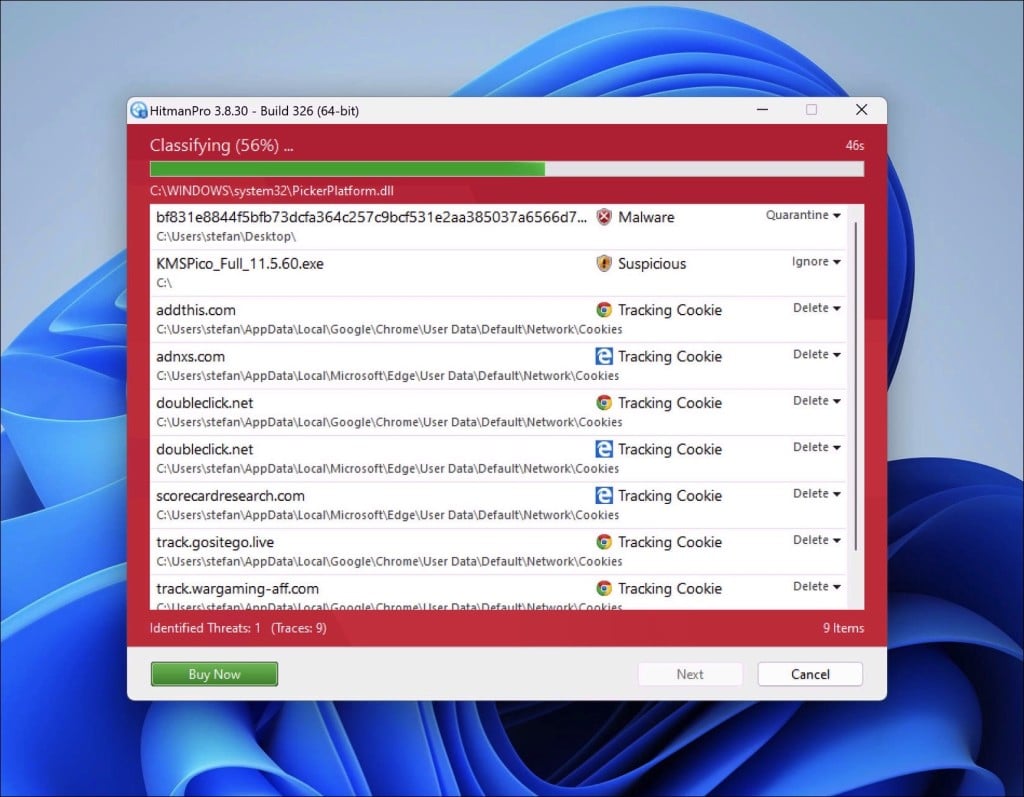
- Sophos HitmanPro will start a malware scan. Once the window turns red, it indicates malware or potentially unwanted programs have been found on your computer during this scan.
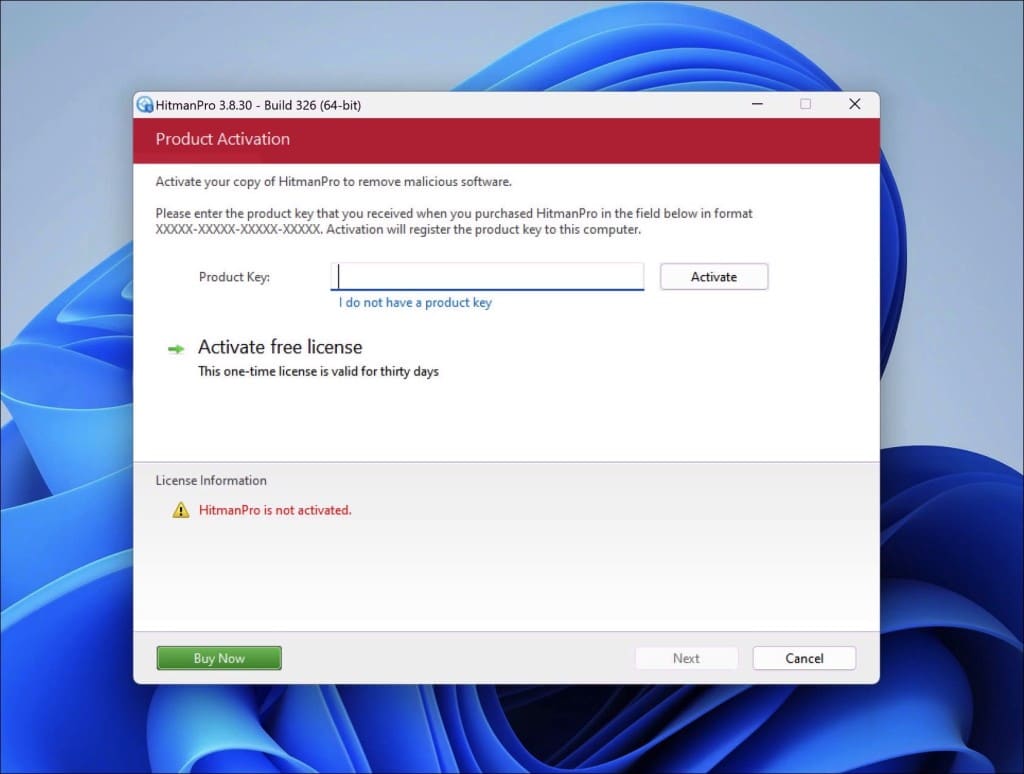
- Before removing the malware detections, you need to activate a free license.
- Click on the “Activate free license.” button.
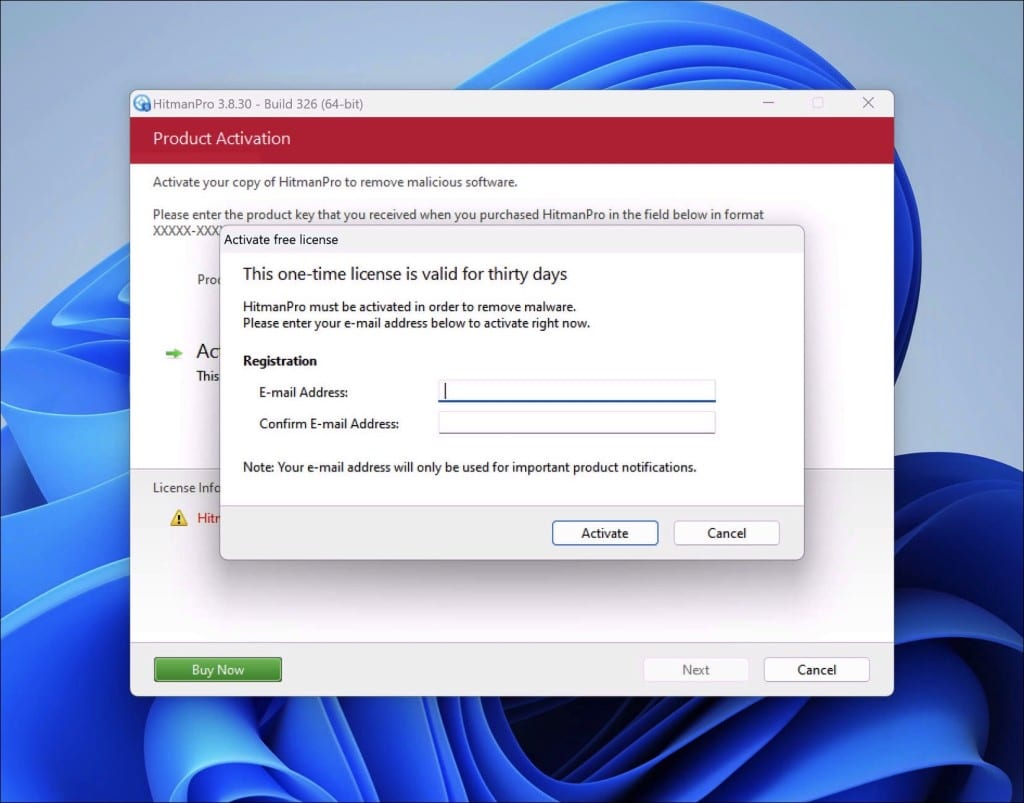
- Provide your e-mail address to activate the one-time license, valid for thirty days.
- Click on the “Activate” button to continue the removal process.
- The HitmanPro product is activated successfully.
- We can now continue with the removal process.
- Sophos HitmanPro will remove all detected malware from your computer. When it is done, you will see a summary of the results.
Adware removal tool by TSA
I have a recommendation that might be your computer’s new best friend. Meet “Adware Removal Tool by TSA.” This nifty little tool is like a Swiss army knife for your browser woes.
Here’s the deal: It’s not just about adware. Have you ever had your browser act weirdly or be taken over by some strange site like the Bitmebx.com crypto scam? Yep, that’s an online scam; this tool can give it the boot. Using Chrome, Firefox, Internet Explorer, or Edge? It’s got you covered across the board.
But wait, there’s more! Clunky toolbars cramping your browsing style? Are malicious extensions sneaking around? TSA’s tool will sweep them away. And if your browser’s acting particularly stubborn, it’s got a reset button that takes everything back to square one—just like the good ol’ days.
The cherry on top? It’s portable—no installation drama. You can even pop it onto a USB or a recovery disk for those “just in case” moments. So, if you need a digital cleanup, give this tool a whirl. It’s handy, accessible, and user-friendly.
Download Adware Removal tool by TSA
Once you start the app, the adware removal tool updates its adware detection definitions. Next, click the “Scan” button to start an adware scan on your computer.
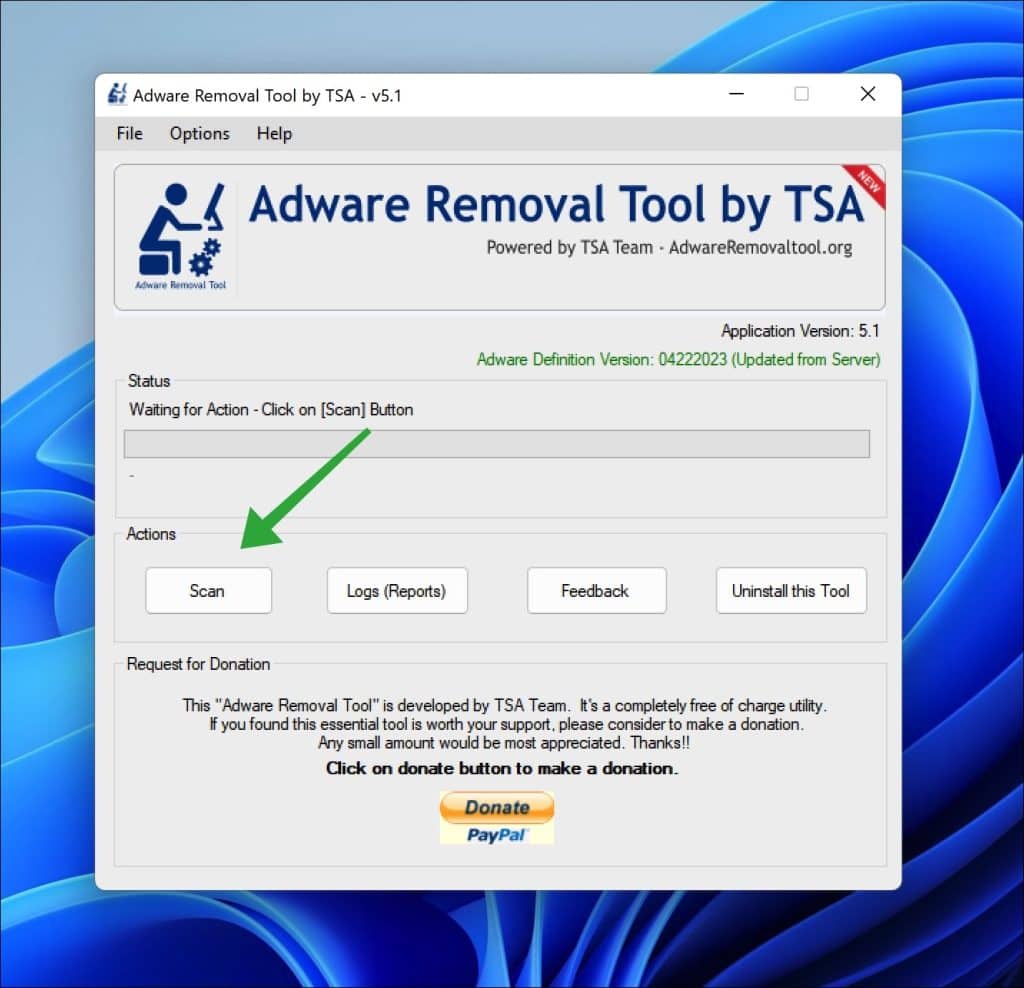
Follow the on-screen instructions to remove detected adware from your PC for free. Next, I advise installing Malwarebytes browser guard to prevent Bitmebx.com ads.
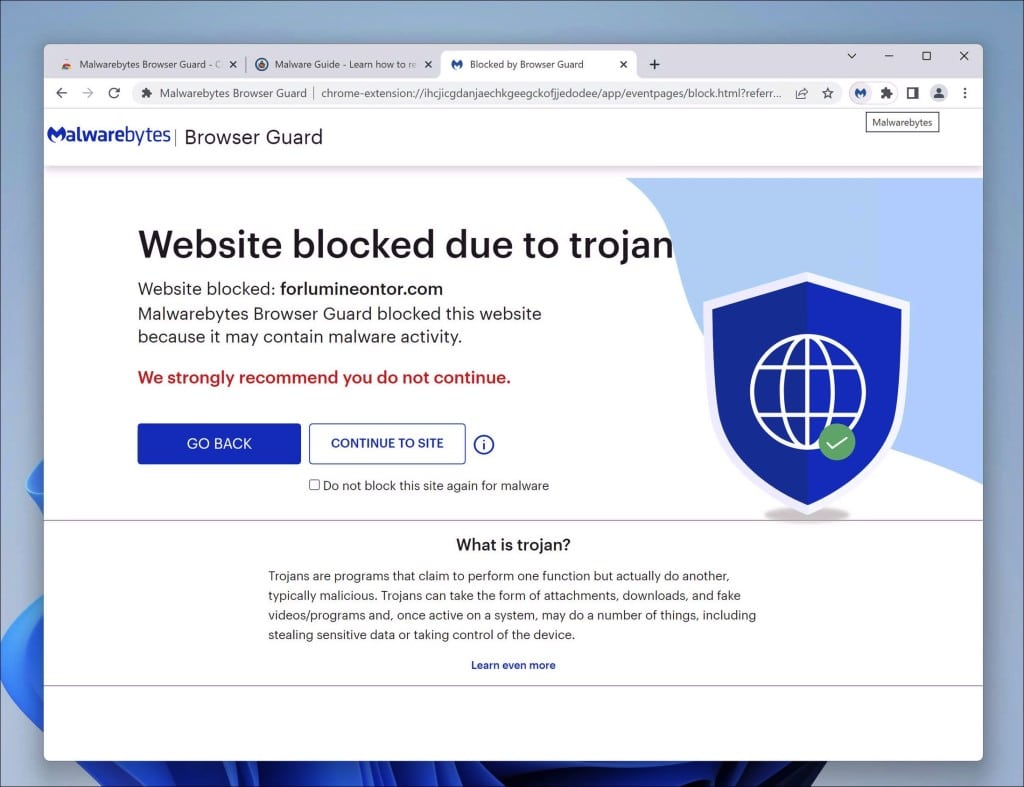
Malwarebytes browser guard
Malwarebytes Browser Guard is a browser extension. This browser extension is available for the most well-known browsers: Google Chrome, Firefox, and Microsoft Edge. When the Malwarebytes browser extension is used, the browser is protected against multiple online attacks—for example, phishing attacks, unwanted websites, malicious websites, and crypto miners.
I recommend installing Malwarebytes browser guard to be better protected against Bitmebx.com now and in the future.
- Download Malwarebytes browser guard.
- Click to install on the preferred browser.
When browsing online, and you might accidentally visit a malicious website, Malwarebytes browser guard will block the attempt, and you will receive a notice.
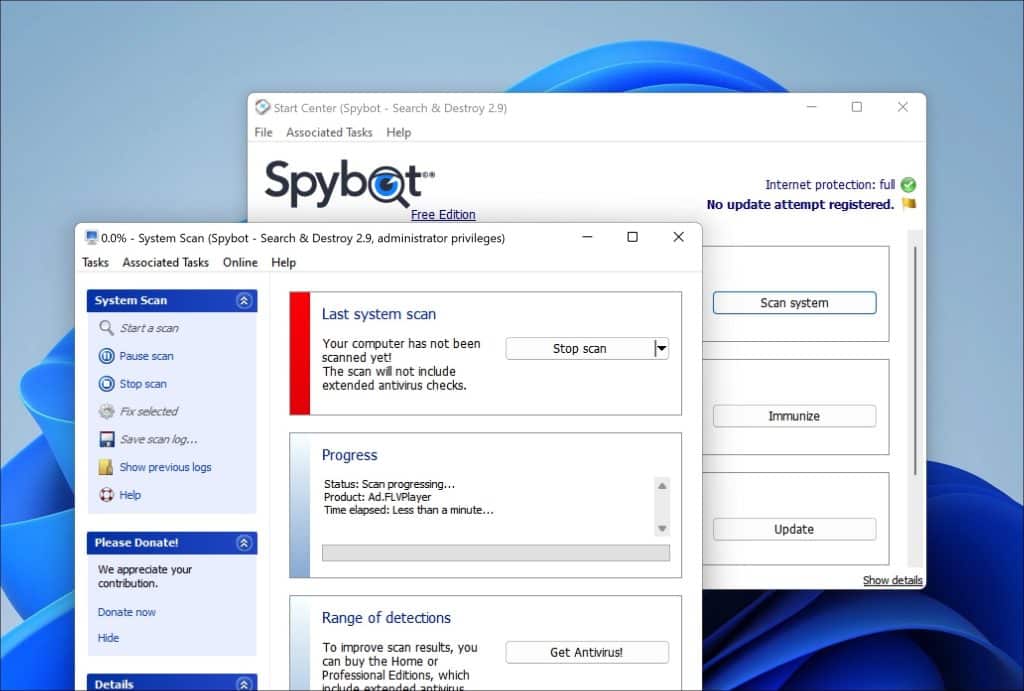
Spybot Search & Destroy
Spybot Search & Destroy is a security software that can safeguard your computer against spyware, adware, and other harmful software. When you use Spybot Search & Destroy, it actively scans your computer’s drive, memory, and registry for any programs or unwanted software. Once it identifies these threats you can easily remove them.
The process begins when you initiate a scan. Spybot Search & Destroy carefully examines your system for any signs of malware, paying attention to tracking cookies, unwanted programs, and web browser hijackers that can compromise your privacy and security.
If it detects anything the software presents a list of these items, for your review.
To eliminate malware from your system you can select the items from the list. Instruct Spybot Search & Destroy to remove them. The software then takes action to clean your system by either deleting these items or isolating them in quarantine based on their nature and potential risk. This proactive approach prevents the malware from operating on your system or accessing your information.
Moreover Spybot Search & Destroy provides immunization features that fortify your systems defenses. By immunizing your system it blocks access to known websites. Prevents unauthorized installation of unwanted programs on your computer. This preventive measure effectively safeguards, against infections.
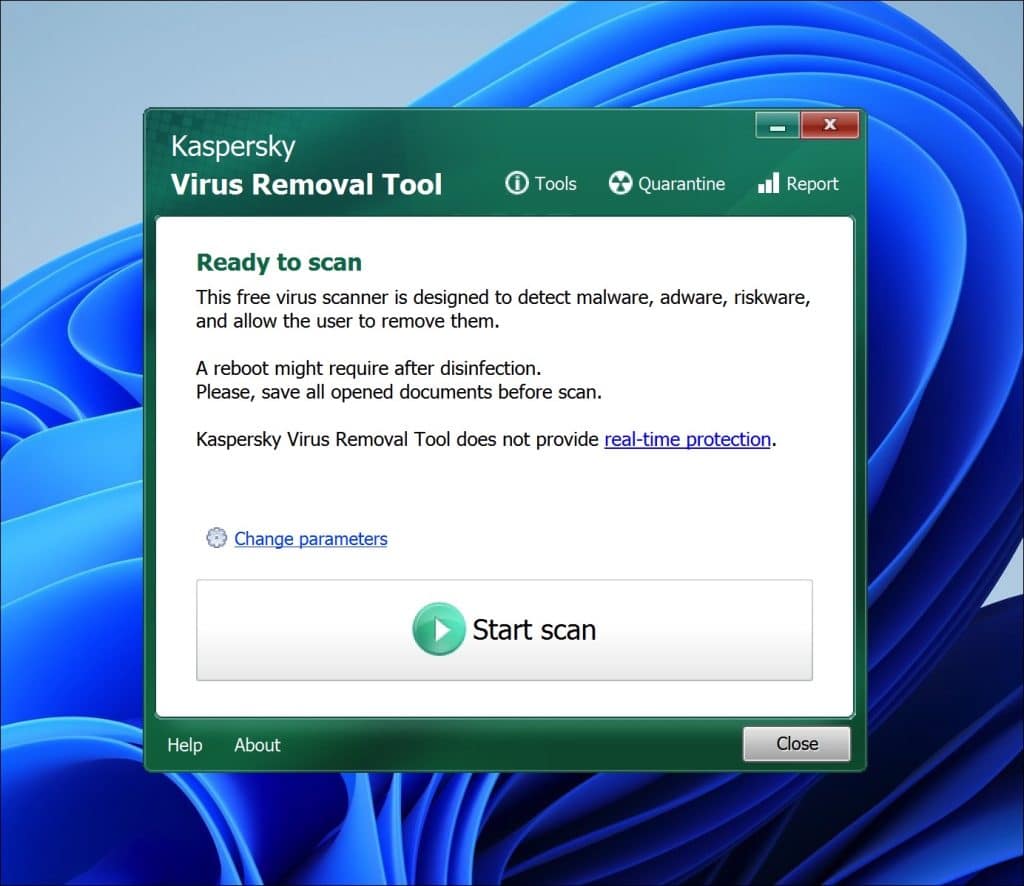
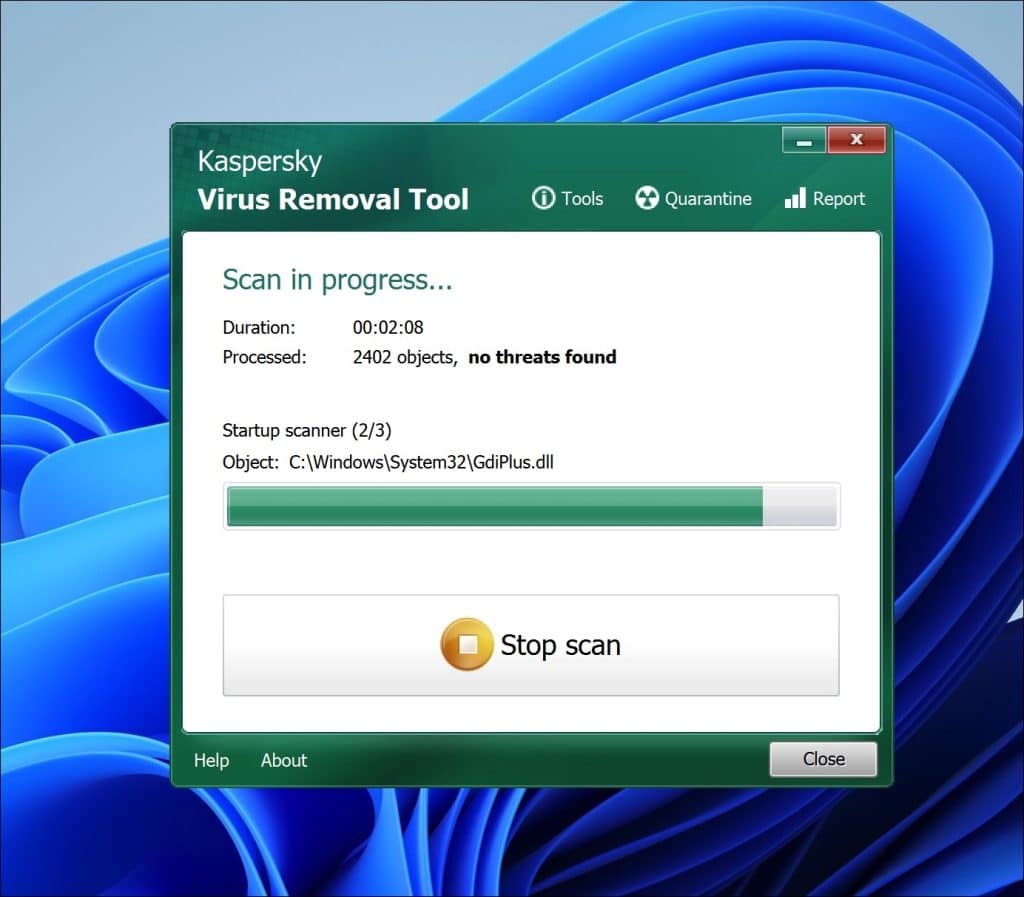
Kaspersky Virus Removal Tool
Kaspersky Virus Removal Tool is a tool that can help you scan and eliminate viruses, Trojans, worms, spyware and other malicious software from your computer. When you use this tool it conducts an examination of your system to uncover and isolate any threats.
After downloading and launching Kaspersky Virus Removal Tool it automatically updates its malware definitions to ensure that it can recognize the threats. You can then initiate a system scan by selecting areas of your computer for checking or opt for a scan that covers every part of your system.
While scanning your computer the tool utilizes detection algorithms developed by Kaspersky to identify malware and other harmful software. If any threats are detected they will be presented in a list with information, about each items nature and level of threat.
To eliminate the malware simply choose the items from the list. Select an action, for Kaspersky Virus Removal Tool to take—typically disinfection (attempting to remove the malware while keeping the infected file intact) deletion (completely removing the file) or quarantine (isolating the file to prevent harm to your system). Kaspersky Virus Removal Tool provides users with the choice of manual disinfection options depending on the severity of the infection and personal preference. Once the malware has been removed it recommends restarting your computer to ensure that the cleaning process is fully completed.
Safeguarding Your Crypto Investments
In the realm of cryptocurrency it’s vital to protect your investments from scams and fraud. By following these steps you can safeguard your assets. Ensure a safe investment journey.
Keep Your Digital Wallets Secure
Your digital wallets are crucial for safeguarding your holdings so it’s important to prioritize their security. Opt for trusted wallets with security features like encryption and multi factor authentication. Regularly update your wallet software to stay protected against hacker exploits.
Choose Established Exchanges
When trading or investing in cryptocurrencies opt for exchanges with reputations. Look for platforms with a history of reliability stringent security protocols and regulatory compliance. Be wary of known exchanges and conduct thorough research before engaging with them.
Activate Two Factor Authentication
Activate two factor authentication (2FA) whenever possible to add a layer of security to your crypto transactions. 2FA requires you to confirm your identity using a device or app such, as a mobile phone or authenticator app before accessing your accounts.
Avoid Using Public Wi Fi for Crypto Transactions
It’s important to steer of public Wi Fi networks when dealing with crypto transactions as they can be susceptible to attacks potentially compromising your sensitive information. Instead, opt for private networks like your home connection or trusted cellular data networks.
Keep Your Software and Antivirus Programs Updated
Make sure to update your operating system, wallet software and antivirus programs to stay protected with the latest security patches against malware and viruses. Cybercriminals are always changing their tactics so its essential to keep your software up to date.
Conduct Comprehensive Research Before Making Investments
To reduce the risk of falling victim to cryptocurrency scams and safeguard your investments it’s crucial to research any cryptocurrency project or token before investing. Take the time to understand its legitimacy and potential risks by examining factors such as the project team, whitepaper, community engagement and regulatory compliance. It’s advisable to rely on sources of information and seek guidance from knowledgeable experts in the field.
By following these practices you can significantly lower the risk associated with crypto scams and protect your valuable investments. Stay vigilant stay informed and embark on a journey, into the world of cryptocurrencies.
| Safeguarding Your Crypto Investments | Key Measures |
|---|---|
| Secure Your Digital Wallets | Use reputable wallets, update software, and enable multi-factor authentication. |
| Use Reputable Exchanges | Choose exchanges with strong security measures and regulatory compliance. |
| Enable Two-Factor Authentication | Add an additional layer of security for your crypto transactions. |
| Avoid Public Wi-Fi for Crypto Transactions | Protect sensitive information by avoiding public Wi-Fi networks. |
| Keep Software and Antivirus Programs Up to Date | Regularly update your software for the latest security patches. |
| Conduct Thorough Research Before Investing | Understand the legitimacy and potential risks of the project or token. |
Understanding the Nature of Crypto Scams
The rise of cryptocurrencies has not brought significant changes but also introduced new risks and challenges. It is crucial to grasp the workings of crypto scams to safeguard your investments and shield yourself from schemes. Crypto scams capitalize on distinctive features of cryptocurrencies including;
- Privacy Concerns; The anonymity offered by cryptocurrencies makes them appealing to scammers who can mask their identities within blockchain networks.
- Transaction Irreversibility; Once a cryptocurrency transaction is validated on the blockchain it becomes nearly impossible to reverse leaving victims with options in case of fraud.
- Absence of Regulation; The decentralized nature of cryptocurrencies means there is no central authority governing transactions resulting in a lack of oversight and heightened susceptibility to scams.
- Complexity in Technology; The intricate technical aspects of cryptocurrencies like keys and digital wallets can be perplexing and daunting for individuals making them more susceptible to fraudulent activities.
- Lucrative Opportunities; While the potential for returns attracts investors it also draws scammers who exploit this desire for financial gains.
- Rapid Expansion of the Industry; The rapid growth pace, in the cryptocurrency sector provides scammers with chances to target unsuspecting investors.
By familiarizing yourself with these aspects you can effectively recognize warning signs remain vigilant and shield yourself from falling victim to crypto scams.
“Investors need to be aware of the risks associated with cryptocurrencies and educate themselves about the potential dangers of crypto scams. Awareness and vigilance are key to protecting your investments in this rapidly evolving industry.” – Crypto Expert
Characteristics of Crypto Scams
| Characteristics | Description |
|---|---|
| Privacy Risks | Scammers leverage the anonymity of cryptocurrencies to hide their identities and carry out fraudulent activities. |
| Irreversibility of Transactions | Once a cryptocurrency transaction is confirmed, it cannot be reversed, leaving victims with little recourse. |
| Lack of Regulation | The decentralized nature of cryptocurrencies means there is no central authority to regulate transactions, making them vulnerable to scams. |
| Technological Complexity | The technical aspects of cryptocurrencies, such as private keys and digital wallets, can be confusing and exploited by scammers. |
| High Profit Potential | Scammers entice victims with promises of significant returns on investments, leveraging the allure of financial gain. |
| Rapid Industry Growth | The fast-paced nature of the cryptocurrency industry provides scammers with ample opportunities to exploit unsuspecting investors. |
Understanding the nature of crypto scams is essential for anyone involved in the cryptocurrency market. By staying informed and adopting a cautious approach, you can safeguard your investments and navigate the crypto landscape securely.
Individual investors and the cryptocurrency market as a whole get hit by schemers. When these swindles work, they create big financial losses for victims. They do even more damage to the trust in virtual moola, and also put a stain on legitimate endeavors. Regulators are forced to step up in response to widespread scams.
The Financial Fall
Crypto scams take everything from you, financially. These cheats are able to convince poor suckers into giving them their hard earned money or other cryptocurrencies that have value. You can kiss your savings goodbye once you’ve fallen into the trap.
Lost Trust In The System
Taking people’s money away from them will cause one thing: distrust. There’s no way somebody would put their faith back into something that just did them dirty. Once a person gets scammed, they’ll tell whoever will listen about it too. This negative word of mouth will plague anyone considering investing in these digital currencies.
Legitimate Projects Take A Beating
Even though not all crypto currencies are trying to rip off their investors, reputations can still be tarnished when scams start getting thrown around. Because crooks know how much hype there is surrounding real projects, they take advantage of branding similarities or false promises to trick people into paying up. Genuine projects then get caught in a wave of doubt and struggle to swim out.
Regulatory Response
You better believe regulators aren’t happy about this either; it makes them look bad! With so many incidents popping up each day, agencies that were built to protect us need to do their job now more than ever before. They’ll be trying harder at implementing regulations that stop frauds like these right in their tracks.
In order for things regarding crypto currency scams to change, vigilance is going to play a key role here. If you think you’re being duped by someone who wants your money but offers no product in return, contact the authorities. From another perspective, industry members need to team up and create a sense of transparency to keep customers happy. Education should be high on the priority list for sure.
FAQ
What is the Bitmebx.com crypto scam all about?
The Bitmebx.com crypto scam is a ploy that targets unsuspecting individuals who invest in the cryptocurrency market. It’s crucial to stay informed about this scam and take measures to safeguard your investments.
What are some types of crypto scams out there?
Various common types of crypto scams include investment frauds, phishing schemes, upgrade hoaxes SIM swap deceptions and counterfeit crypto exchanges and wallets. Understanding these scams is vital for protecting your assets.
What risks come with investing in cryptocurrencies?
Investing in cryptocurrencies carries risks due to the industrys lack of regulation, technological complexities and rapid expansion. Being aware of these risks and taking precautions when entering into investments is essential.
What signs should I watch out for to identify crypto scams?
Signs indicating crypto scams include demands for payments exclusively in cryptocurrencies, promises of guaranteed returns blending investment advice with online dating interactions requests, for cryptocurrency access keys and receiving suspicious texts or emails impersonating reputable organizations.
How can I go about reporting a suspected scam if I’ve been affected by one?
In that situation it is crucial to inform the authorities like the Federal Trade Commission, Securities and Exchange Commission, Commodity Futures Trading Commission or the Internet Crime Complaint Center.
What are some recommended practices for avoiding cryptocurrency scams?
To steer clear of cryptocurrency scams investors should refrain from responding to communications verify links and attachments before clicking on them maintain separate accounts flag any unusual activity choose reputable companies and look for “https” in website URLs.
How can I protect my cryptocurrency investments?
Protecting your cryptocurrency investments involves securing your wallets using trusted exchanges enabling two factor authentication avoiding public Wi Fi for transactions involving cryptocurrencies keeping software and antivirus programs updated regularly and conducting thorough research before making any investments.
What factors contribute to the nature of cryptocurrency scams?
The characteristics of cryptocurrency scams are shaped by factors like privacy vulnerabilities, irreversible transactions, lack of oversight, technological intricacies, potential for high profits and rapid growth of the industry.
What impact do cryptocurrency scams have?
Cryptocurrency scams have an impact, on both individual investors and the overall crypto market.
Crypto scams can lead to losses for those affected a decline in trust within the cryptocurrency market harm to the reputation of legitimate projects and heightened regulatory oversight.
What steps can I take to learn more about crypto scams and help others do the same?
Learning about crypto scams and educating others can involve raising awareness sharing experiences advocating for anti scam laws and promoting safe investment strategies.
How can I shield my investments from schemes like the Bitmebx.com crypto scam?
Protecting your investments from scams, like Bitmebx.com involves staying informed being educated on scam tactics identifying warning signs reporting any activity and implementing protective measures.
Thank you for reading!