Every passing day makes ransomware attacks more normal. They create havoc and demand a monetary payout from victims. The latest addition is HEDA ransomware. This troublesome software claims all your personal files and forces you to pay up to regain access.
We gathered the most crucial information about this malware: how it works, ways to identify an attack, and what to do if you’re a victim. By being proactive in prevention and knowing the right steps if afflicted, you can minimize the virus’s effects.
What is HEDA Ransomware?
HEDA ransomware is not your ordinary virus; it’s a sophisticated form of malicious software that employs encryption techniques to lock users out of their files and documents. This encryption takes your data hostage, with the attackers demanding a ransom, typically in the form of Bitcoin cryptocurrency, to supposedly unlock your files. The ransom amount is not static and can vary depending on the specific variant of the HEDA ransomware.
The Manifestation of HEDA Ransomware on Your System
When a system falls prey to this ransomware, the aftermath is quite discernible:
- Encryption of Files: Your essential documents, photos, databases, and more become encrypted and rendered inaccessible.
- File Extension Alteration: In a clear sign of its presence, the ransomware appends a distinct string to affected file extensions. For example, what was once “presentation.ppt” would now appear as “presentation.ppt.HEDA”.
- Ransom Note: A surefire indicator of the ransomware’s presence is the appearance of a text file, usually named “DECRYPT-FILES.txt.” This file, often found on the Windows desktop, contains the ransom note detailing the ransom amount and payment procedures.
The dilemma facing victims of the HEDA ransomware is substantial. In many scenarios, recovering encrypted files without the cooperation of the ransomware’s creators is a herculean task. There have been instances where ransomware developers have accidentally left flaws in their encryption mechanisms, providing a potential recovery window. However, banking on such a loophole is uncertain and rare.
To Pay or Not to Pay
One of the most pressing questions facing victims is whether to pay the ransom. Succumbing to the demands of cybercriminals, however, is fraught with issues:
- No Guarantees: Paying the ransom doesn’t assure the safe return of your files. There’s a significant risk that the files remain locked even after payment, or worse, the malware might still linger.
- Fueling Criminal Endeavors: Giving in to the ransom demands indirectly promotes cybercriminal activities, emboldening them and funding their future ventures.
- Setting a Precedent: Paying once can make you a repeat target for cybercriminals.
Considering these risks, the prudent course of action is to refrain from paying. Instead, one’s best defense against such threats is a robust, regularly updated backup system. If you have an untouched backup of your Windows system and files, you can restore your data, effectively negating the ransomware’s grip on your system.
Guarding Against Future Ransomware Attacks
To guard against the sinister clutches of ransomware, adopting a proactive, multi-pronged strategy is essential:
- Regular Backups: Consistently back up your data to local storage and cloud-based solutions. Ensure these backups are periodically tested for reliability.
- Software Updates: Regularly update your operating system and all software. Cybercriminals often exploit known vulnerabilities in outdated software.
- Email Vigilance: Be wary of unsolicited emails, especially those with attachments or links. Often, ransomware spreads through phishing campaigns or malicious email attachments.
- Trustworthy Security Software: Equip your system with reliable, updated security software that offers real-time protection.
- Educate and Inform: Regularly train and inform yourself and others about emerging threats and the importance of cautious online behavior.
- Avoid Suspicious Downloads: Refrain from downloading files from unknown sources or dubious websites.
How to Remove HEDA Ransomware virus
When ransomware like HEDA takes root, it encrypts your files and documents, rendering them inaccessible. The decryption key, essential to unlocking these files, is typically held hostage on the attackers’ server. The perpetrators then demand a ransom, usually in cryptocurrency, for this key.
However, even if you’re inclined to consider paying, remember that the cybercriminals have no real obligation to provide the decryption key after receiving the ransom. Moreover, you’re indirectly endorsing and funding these illicit activities by paying.
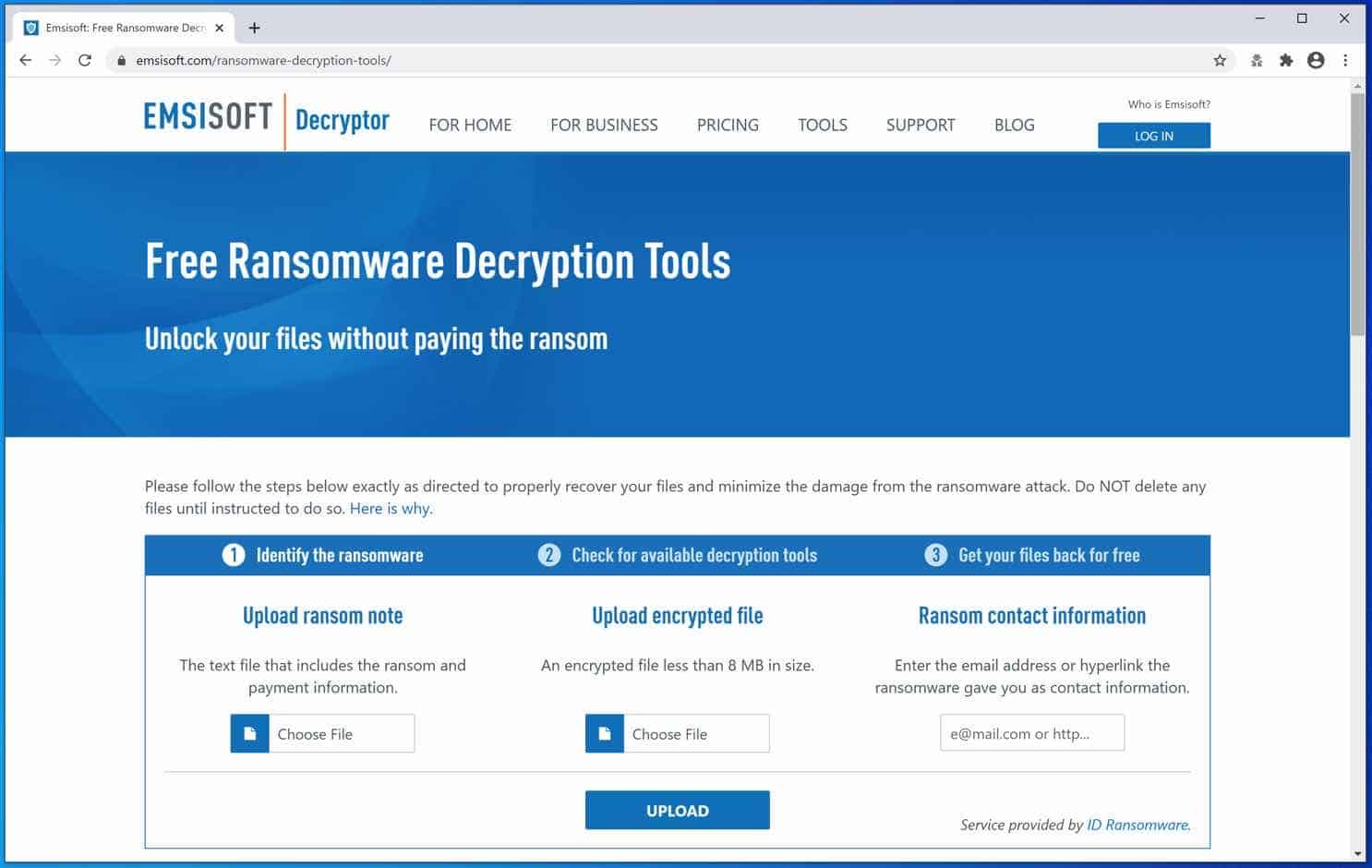
One potential avenue for file restoration is the ID Ransomware suite of decryption tools. This platform attempts to identify the specific ransomware strain that has affected your computer.
- Uploading a File: Navigate to the ID Ransomware website and upload one of your encrypted files. This platform will analyze the file to determine the ransomware variant.
- Ransomware Identification: If the platform recognizes the ransomware strain, it will provide you with available decryption tools or solutions, if any exist.
- Apply Decryption: Follow the instructions carefully if a decryption solution is available. Remember, always backup your encrypted files before attempting any decryption to preserve them in their current state in case the process fails or causes further issues.
Removing the HEDA Ransomware
Before considering potential file restoration options, the first step should always be removing the malicious software. For this task, several robust anti-malware tools are available, and among the most reputable is Malwarebytes.

If a HEDA ransomware decryption tool is available on the NoMoreRansom site, the decryption information will show you how to proceed. Unfortunately, this rarely works out, but it is worth the try.
You can also use the Emsisoft ransomware decryption tools.
Remove HEDA Ransomware with Malwarebytes
Note: Malwarebytes will not restore or recover your encrypted files. However, it removes the HEDA virus file that infected your computer with the HEDA ransomware and downloads the ransomware file to your computer, known as the payload file.
It is essential to remove the ransomware file if you are not reinstalling Windows. By doing so, you will prevent your computer from another ransomware infection.
Install Malwarebytes, and follow the on-screen instructions.
Click Scan to start a malware scan.
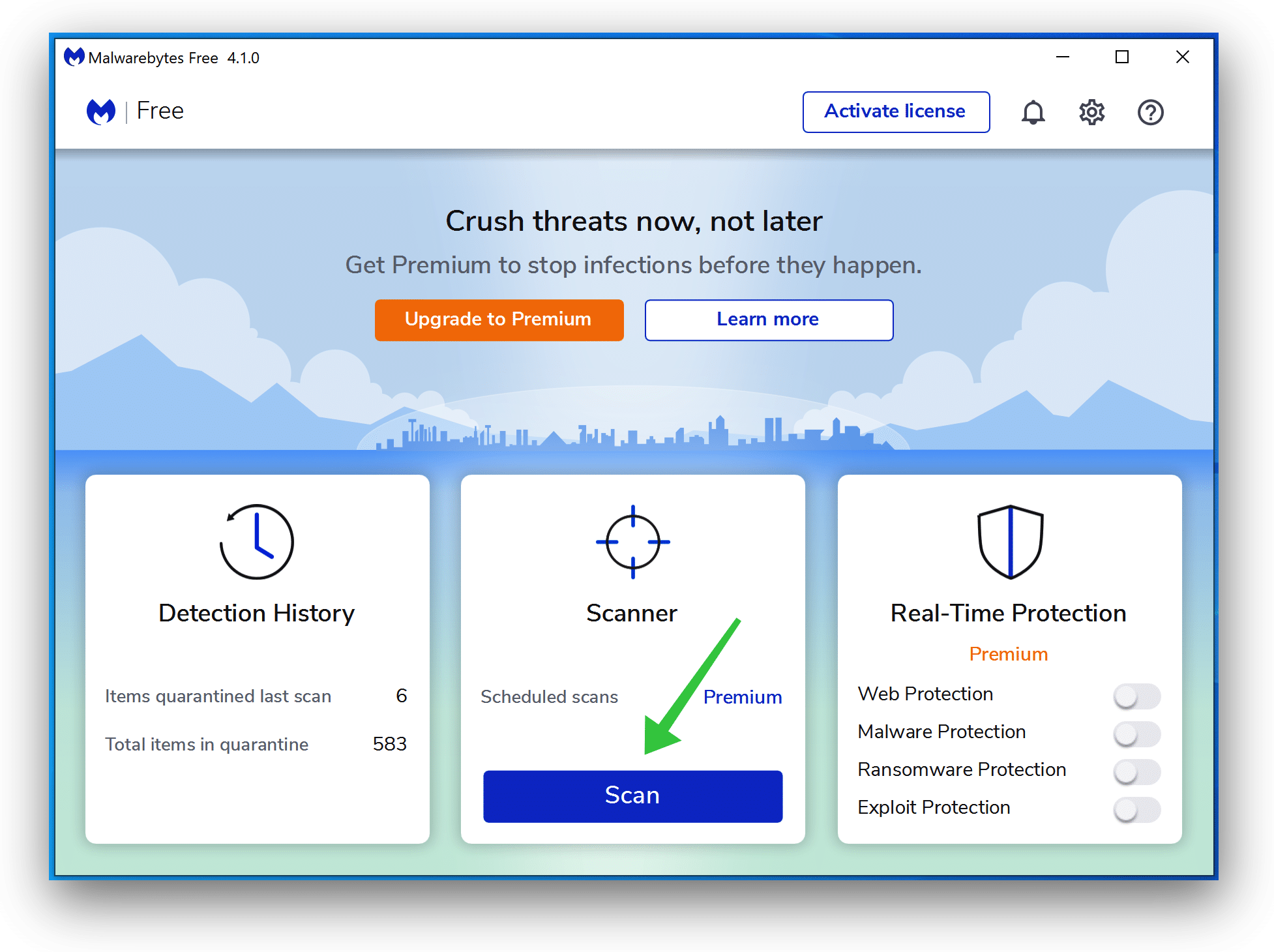
Wait for the Malwarebytes scan to finish.
Once completed, review the HEDA ransomware detections.
Click Quarantine to continue.
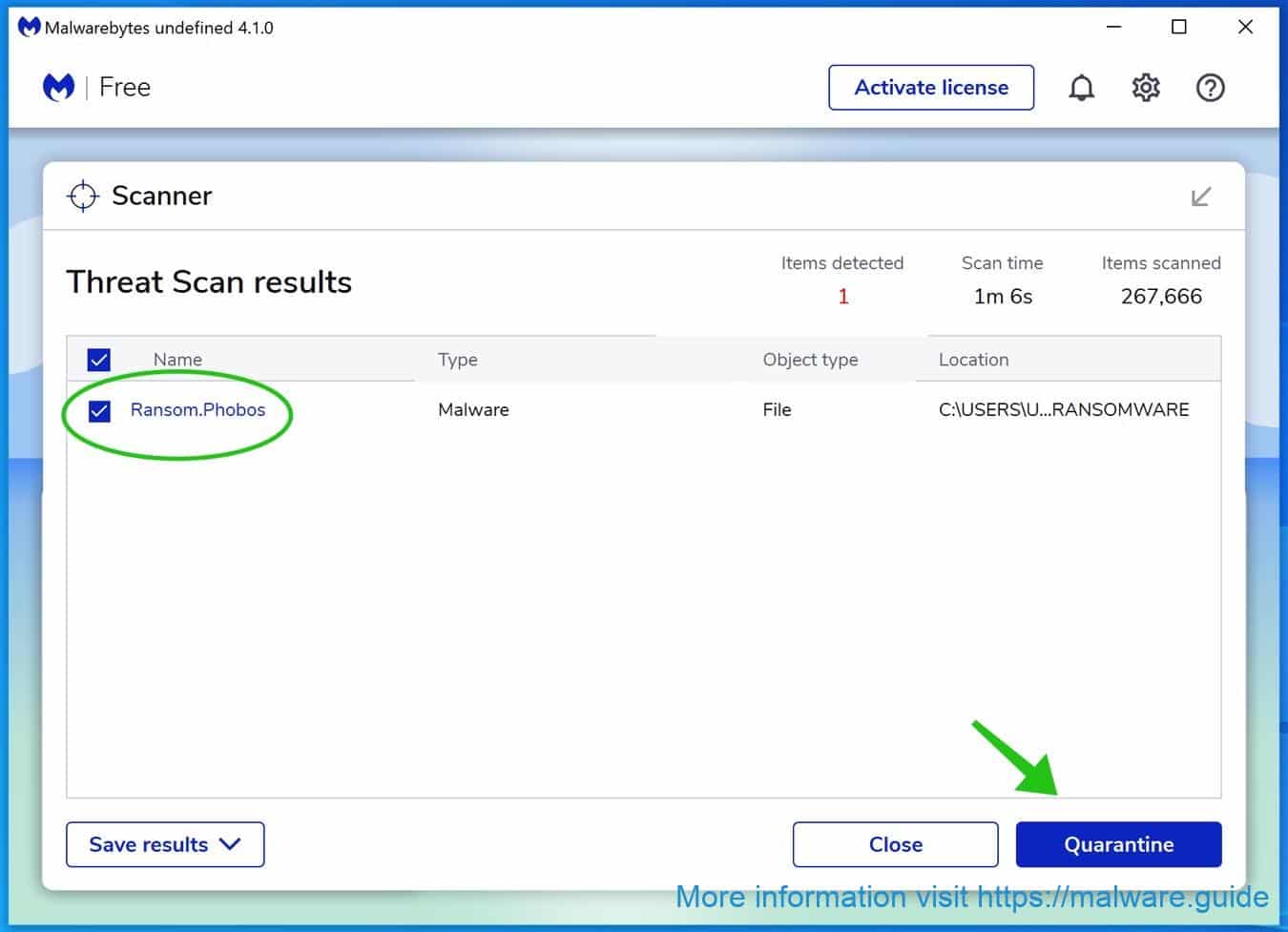
Reboot Windows after all the detections are moved to quarantine.
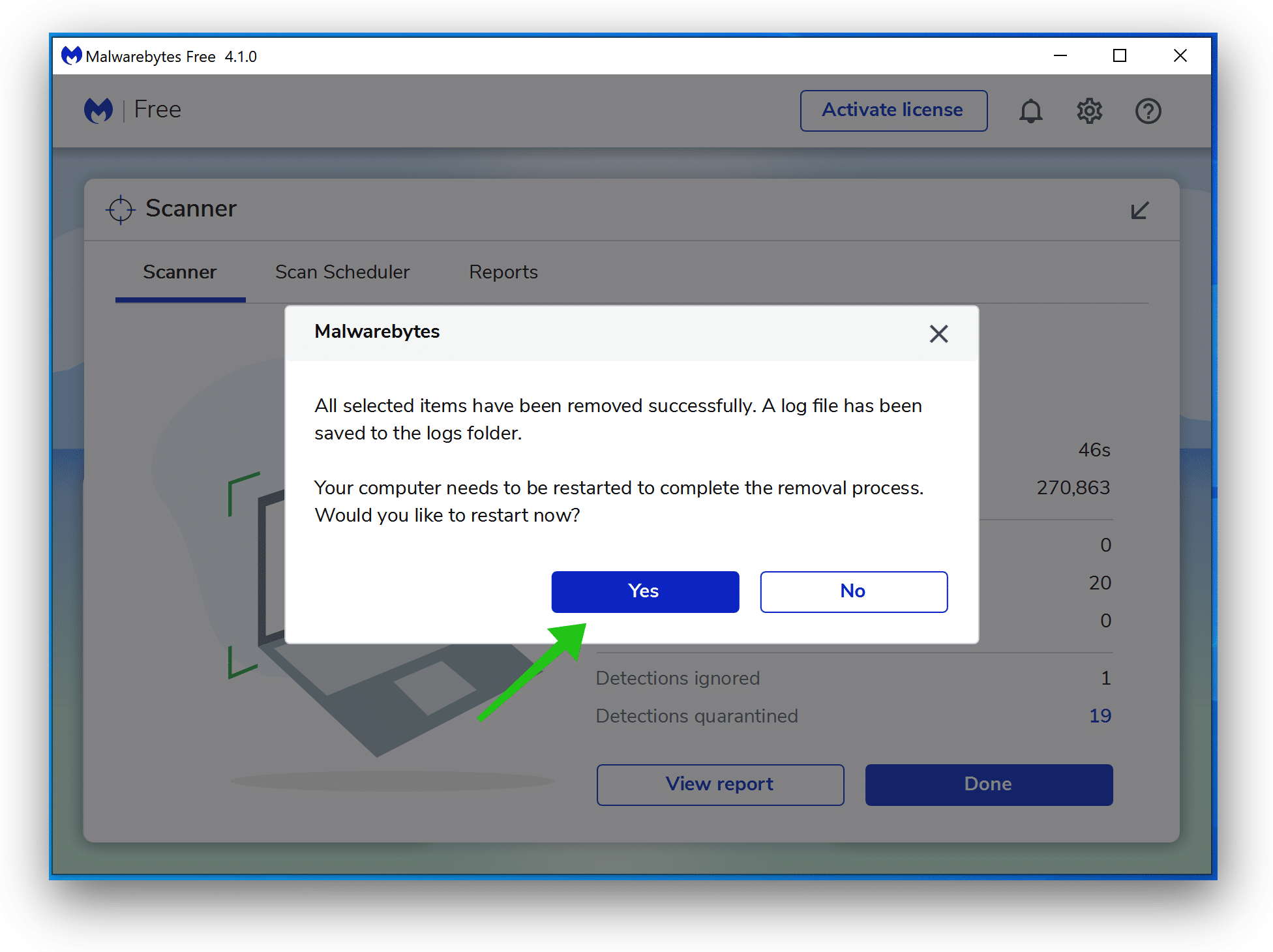
You have now successfully removed HEDA Ransomware file from your device.
Combo Cleaner
Combo Cleaner is a cleaning and antivirus program for Mac, PC, and Android devices. It is equipped with features to protect devices from various types of malware, including spyware, trojans, ransomware, and adware. The software includes tools for on-demand scans to remove and prevent malware, adware, and ransomware infections. It also offers features like a disk cleaner, big files finder (free), duplicate files finder (free), privacy scanner, and application uninstaller.
Follow the installation instructions to install the application on your device. Open Combo Cleaner after installation.
- Click the "Start scan" button to initiate a malware removal scan.
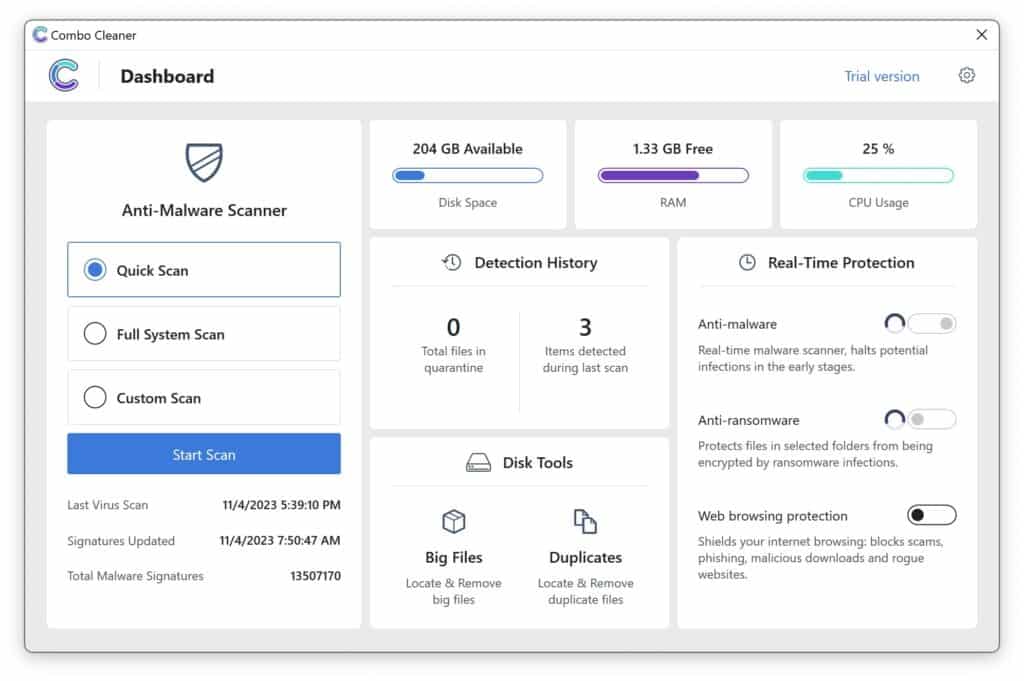
- Wait for Combo Cleaner to detect malware threats on your computer.
- When the Scan is finished, Combo Cleaner will show the found malware.
- Click "Move to Quarantine" to move the found malware to quarantine, where it can't harm your computer anymore.
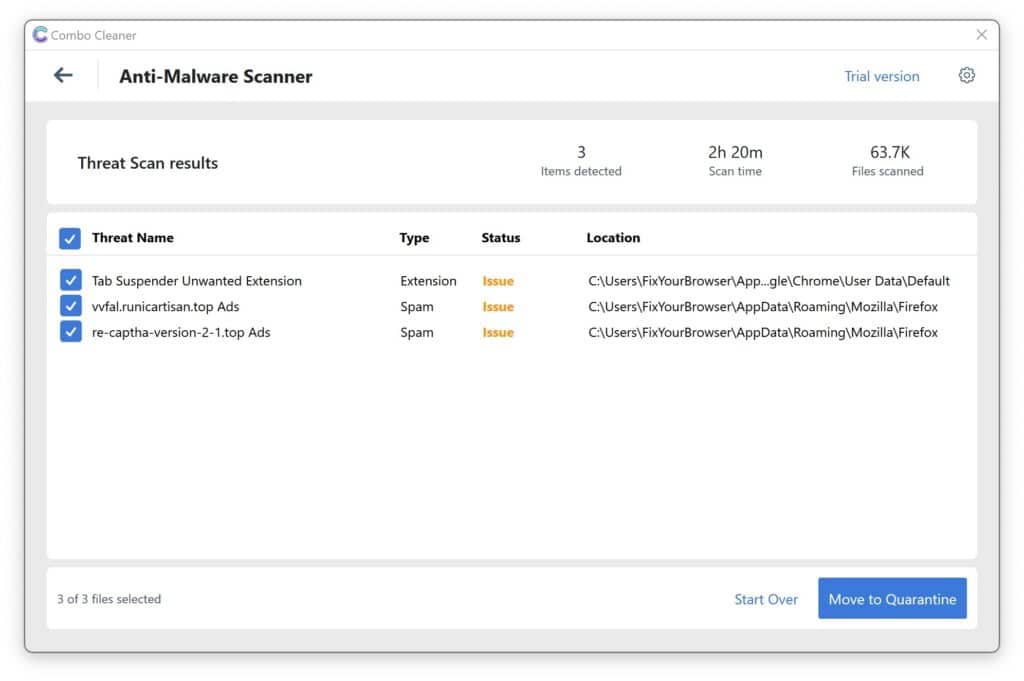
- A malware scan summary is shown to inform you about all threats found.
- Click "Done" to close the scan.
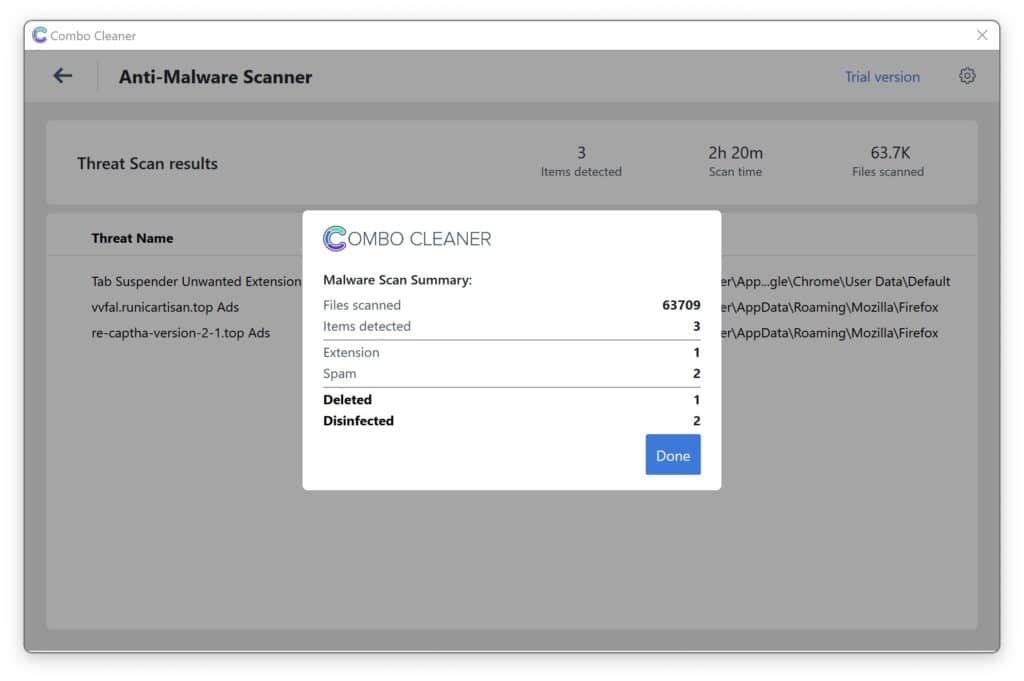
Use Combo Cleaner regularly to keep your device clean and protected. Combo Cleaner will remain active on your computer to protect your computer from future threats that try to attack your computer. If you have any questions or issues, Combo Cleaner offers a dedicated support team available 24/7.
 Remove malware with Sophos HitmanPRO
Remove malware with Sophos HitmanPRO
In this second malware removal step, we will start a second scan to ensure no malware remnants are left on your computer. HitmanPRO is a cloud scanner that scans every active file for malicious activity on your computer and sends it to the Sophos cloud for detection. In the Sophos cloud, both Bitdefender antivirus and Kaspersky antivirus scan the file for malicious activities.
Understanding the Power of HitmanPRO
HitmanPRO is not just any scanner; it stands out for several reasons:
- Cloud-Based Scanning: Instead of relying solely on your computer’s resources, HitmanPRO uses the cloud to scan files, ensuring that your system remains unburdened and that the scan leverages up-to-date threat databases.
- Multi-Engine Verification: Once a suspicious or active file is identified on your computer, it is promptly sent to the Sophos cloud. Here, not one but two renowned antivirus engines—Bitdefender and Kaspersky—meticulously scan the file. This dual-layer scrutiny ensures a higher detection rate and reduces the likelihood of false positives.
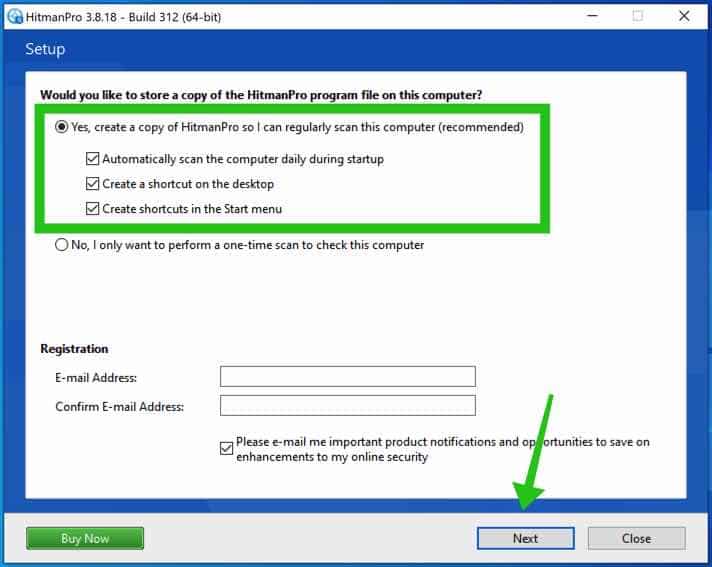
When you have downloaded HitmanPRO, install the HitmanPro 32-bit or HitmanPRO x64. Downloads are saved to the Downloads folder on your computer.
Open HitmanPRO to start the installation and scan.

Accept the Sophos HitmanPRO license agreement to continue. Read the license agreement, check the box, and click on Next.
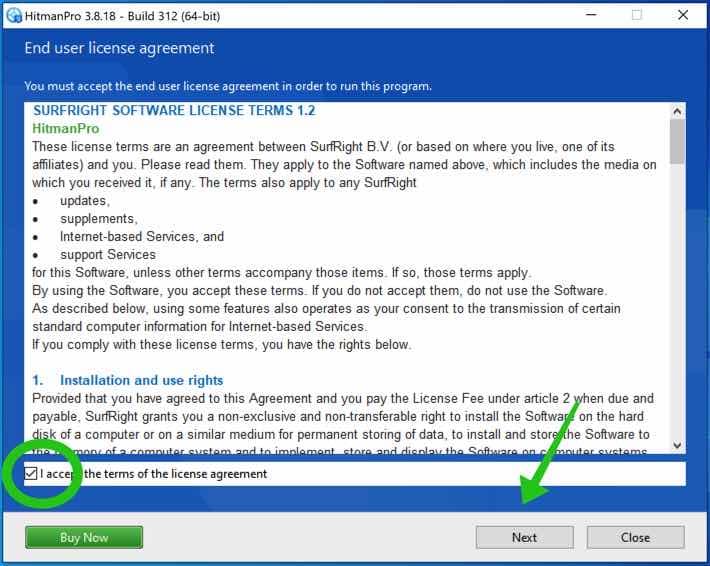
Click the Next button to continue Sophos HitmanPRO installation. Make sure to create a copy of HitmanPRO for regular scans.
HitmanPRO begins with a scan. Wait for the antivirus scan results.
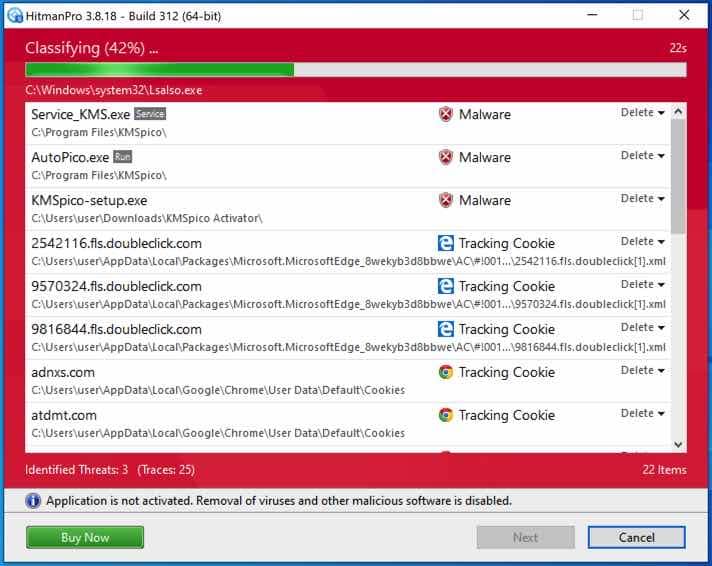
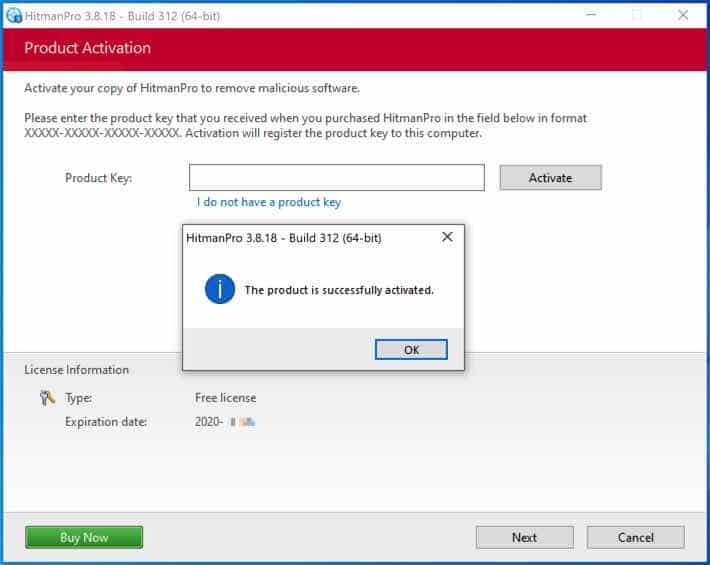
When the scan is done, click Next and activate the free HitmanPRO license. Click on Activate Free license.
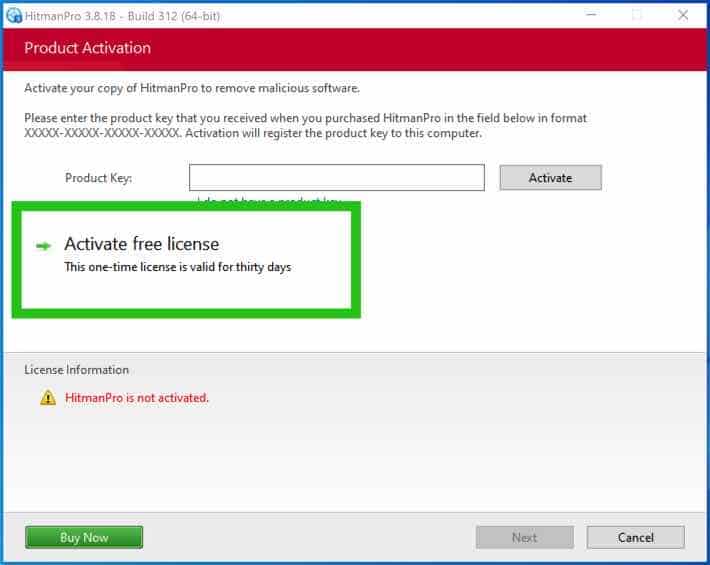
Enter your e-mail for a Sophos HitmanPRO free thirty days license. Click on Activate.
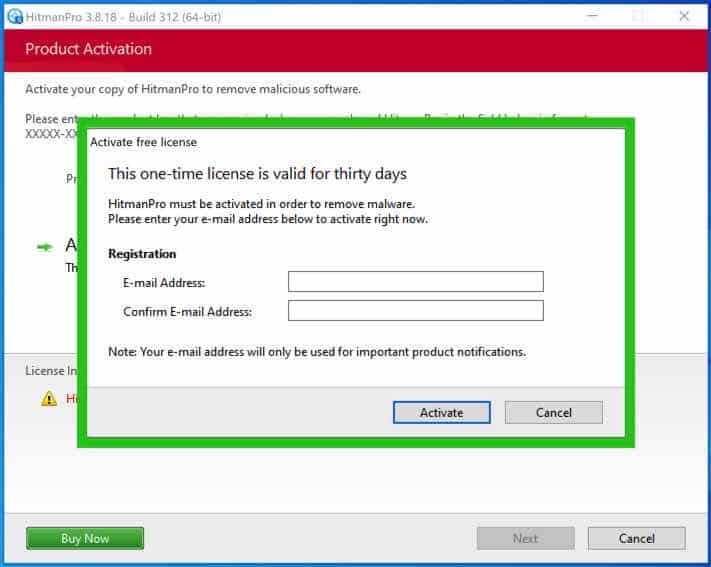
The free HitmanPRO license is successfully activated.
You’ll be presented with the HEDA ransomware removal results. Click Next to continue.
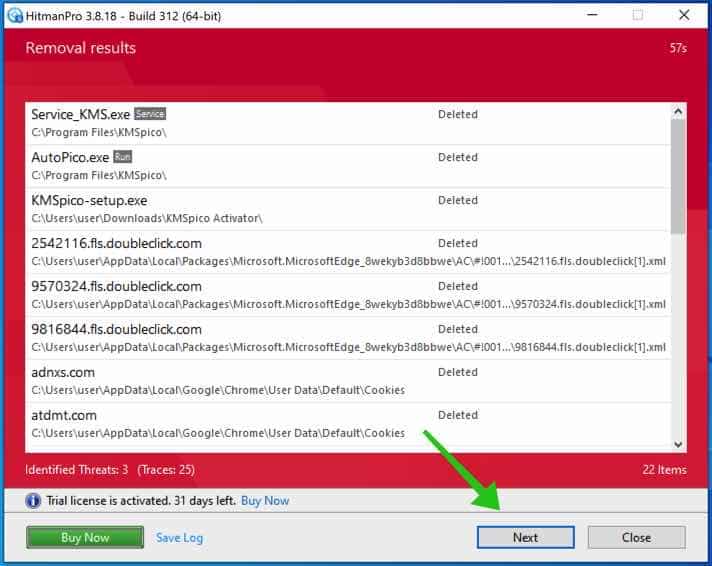
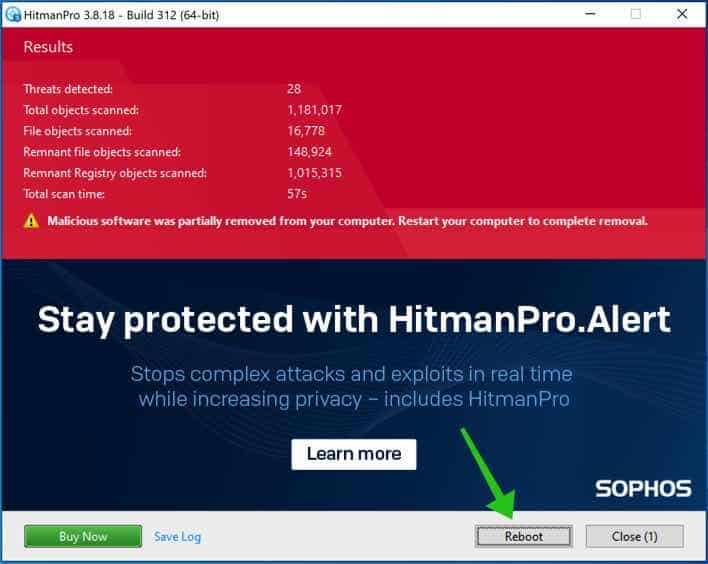
Malicious software was partially removed from your computer. Restart your computer to complete the removal.
What is HEDA ransomware?
The HEDA Ransomware is malicious software that locks or encrypts data on a computer or network. It is known as ransomware because it demands a ransom payment for the user to be able to access their data again. The virus is usually spread through malicious links or attachments sent via email or other messaging services. Once installed, the ransomware will encrypt the user’s data, making it inaccessible. The user will then be presented with a ransom message demanding payment to receive a key that will allow them to decrypt the data. Unfortunately, no guarantee paying the ransom will work, as there is no guarantee that the attackers will provide the key. Therefore, it is important to protect yourself from ransomware and ensure that your data is backed up regularly in case of an attack.
How did my computer get infected with HEDA ransomware?
Ransomware is one of the more insidious forms of a computer virus, as it can infect computers quickly and silently. In most cases, ransomware is spread via malicious email attachments or links to malicious websites that download the virus onto the computer. It can also be spread through software downloads, USB drives, and other devices. Once downloaded, ransomware will typically encrypt the files on the computer, making them inaccessible unless the user pays a ransom.
In some cases, ransomware will also delete or corrupt essential system files, making the computer unusable until the ransom has been paid. Since ransomware is so difficult to remove, it’s important to take preventative measures, such as keeping your computer updated with the latest security updates and using a good antivirus program to detect and remove any malicious files.
How to prevent HEDA ransomware?
Ransomware is an increasingly common type of virus that can cause serious damage to your computer and data. If a ransomware virus infects your device, it can lock up your files and demand you pay a ransom to regain access. Fortunately, there are steps you can take to protect yourself and your data from ransomware. First and foremost, you should always ensure your computer is running the latest version of its operating system and security software. You should also be wary of suspicious emails and attachments, as hackers often use them to spread malware.
Creating regular data backups to restore your computer if infected is also essential. Finally, knowing the different types of ransomware and how they work is a good idea. By taking these steps, you can help to protect yourself and your computer from becoming a victim of ransomware.
Malwarebytes is an antivirus program that protects your computer from malicious software such as ransomware. Ransomware is malware that encrypts your files and holds them hostage until you pay a fee. It can be extremely difficult to remove, so having a good antivirus program like Malwarebytes is essential. Malwarebytes is designed to detect, quarantine, and remove ransomware before it can cause any damage. It also has real-time protection, detecting ransomware before it gets to your computer. On top of that, it has a powerful malware scanner that can detect and remove any malware, including ransomware. So if you’re looking for an antivirus program to protect your computer from ransomware, Malwarebytes is an excellent choice.
Learn more about Malwarebytes and how it protects your computer against ransomware.
I hope this helped. Thank you for reading!