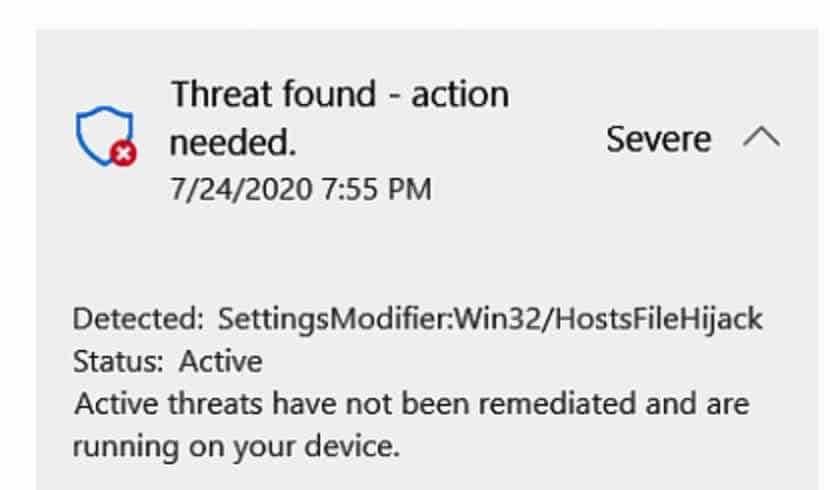
This SettingsModifier:Win32/HostsFileHijack (Windows Defender Antivirus) detection flags suspicious modifications to the Windows hosts file, specifical records for certain domains used by the operating system, and critical windows services. Windows uses the hosts files to resolve domains to IP addresses during network connection, so malicious adjustments can prevent legitimate network connections, such as updates and certificate checks, or result in unsafe and potentially dangerous network connections.
Hosts file tampering is a popular malware or attacker method used to block or redirect network connections. An attacker might change the file to block certain legitimate connections or to redirect network traffic to a destination controlled by the attacker, resulting in the download of extra malware or other malicious activity.
As a result of the SettingsModifier Win32 HostsFileHijack detection you might notice some applications or even Windows activation scripts stop working. Windows Defender will remove the entries in the HOSTS file if you allow it to. You can also deny the detection by clicking the Allow on the device button and exclude the detection in Windows Defender Antivirus.
Remove SettingsModifier:Win32/HostsFileHijack
 Remove SettingsModifier:Win32/HostsFileHijack with Malwarebytes
Remove SettingsModifier:Win32/HostsFileHijack with Malwarebytes
I do advise you to scan your computer with Malwarebytes for malicious malware entries to maybe without your consent have edited the Windows HOSTS file on your computer. If you do know you edited the HOSTS entries yourself you should also scan your computer for malware. Don’t worry, Malwarebytes is free to use for 14 days to detect and remove malware.
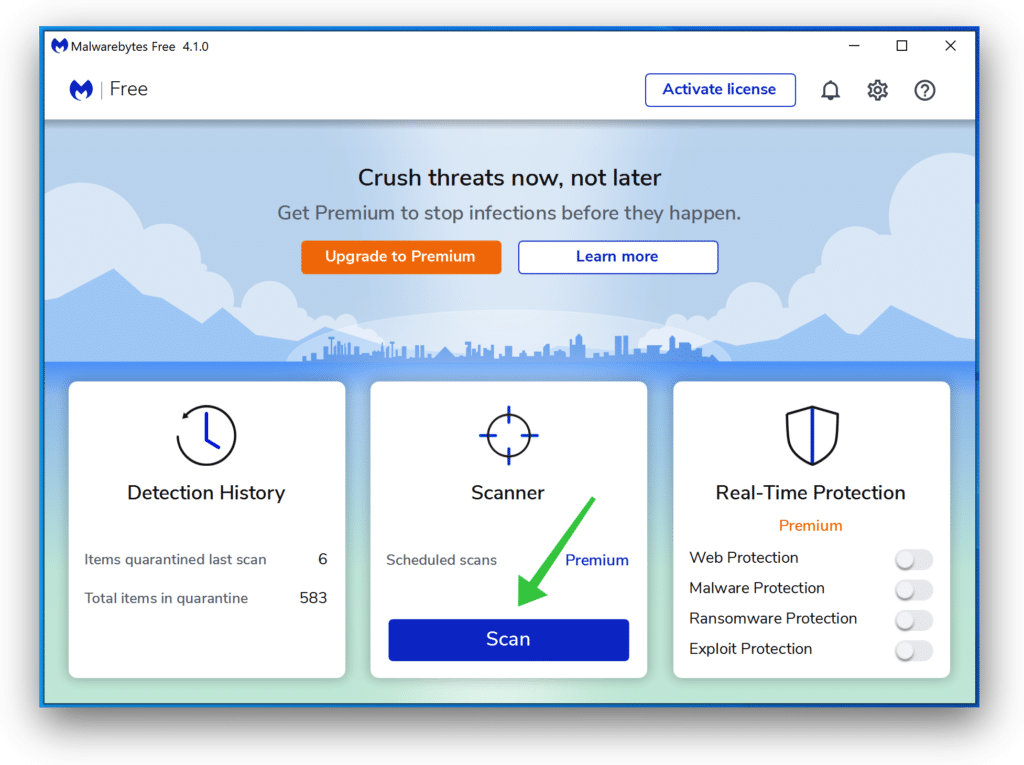
- Install Malwarebytes, follow on-screen instructions.
- Click Scan to start a malware-scan.
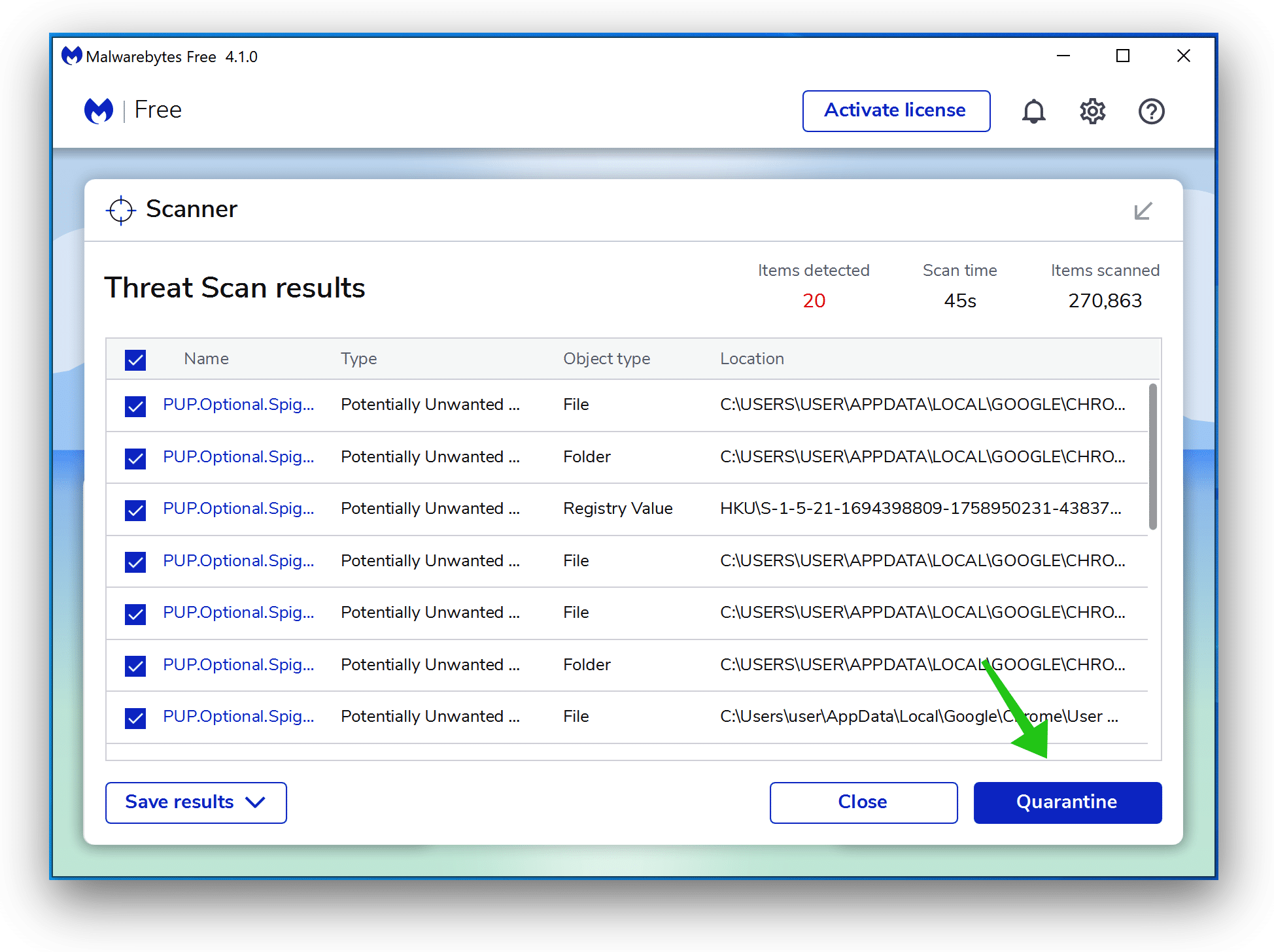
- Wait for the Malwarebytes scan to finish.
- Once completed, review the SettingsModifier:Win32/HostsFileHijack detection(s).
- Click Quarantine to continue.
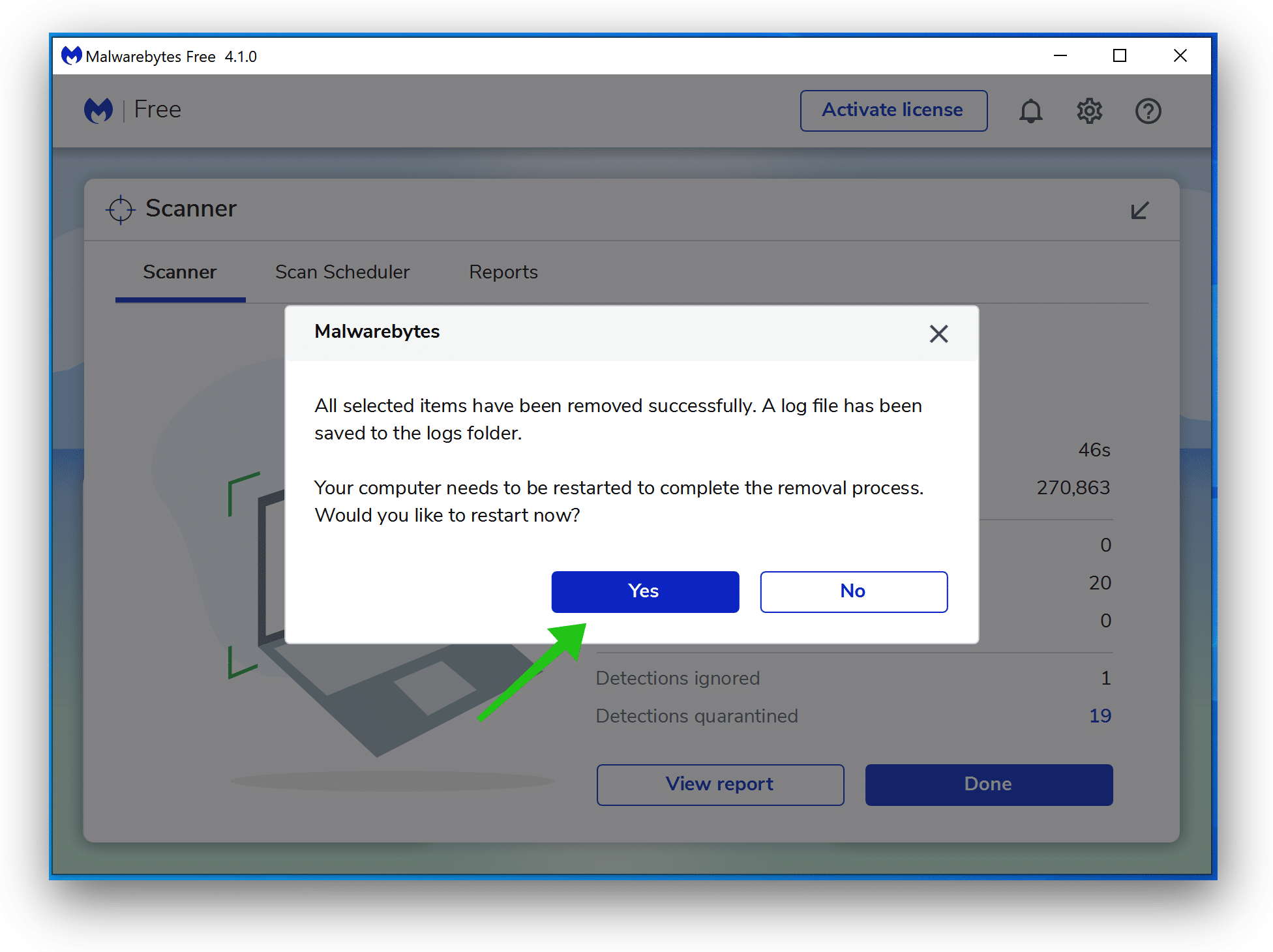
-
- Reboot Windows after all the detections are moved to quarantine.
You have now successfully removed SettingsModifier:Win32/HostsFileHijack from your device.