How can you remove a virus file called Trojan.Injector? Trojan.Injector is a type of file that infects computers. It takes control of your computer, collects information, and can even be used by hackers to gain access to your system.
If your antivirus software detects the presence of Trojan.Injector it means that some related files still remain. These remaining files associated with Trojan.Injector should be deleted. However antivirus programs often struggle to eliminate all traces of Trojan.Injector.
The Trojan.Injector virus is a form of code created to infect computers or network systems causing damage, disruption or data theft. It can spread from one computer to another. Can even impact entire networks. Computer viruses can be transmitted through downloads storage devices like USB drives and even email attachments. Over time these malicious threats have become increasingly sophisticated making it challenging for users to detect and safeguard their systems against attacks. Different types of computer viruses exist, each possessing its characteristics and capabilities that can lead to severe consequences when they infect any device or system.
Users must grasp the risks associated with computer viruses and take measures to safeguard their data against these harmful intrusions.
A computer virus is any software intentionally created to infect computers by causing damage, to data or disrupting normal operations.
Computer viruses can propagate through networks and removable media like USB drives. They can also be transmitted as email attachments. Some viruses even can self replicate and infect computers without any human intervention. There exist types of computer viruses and malicious software including worms, Trojans and other forms of malware. These nefarious entities are often engineered to cause damage or disruption to computer systems and networks pilfer information or corrupt data. Viruses and other forms of malware can be disseminated through files, websites, email attachments and other executable code formats.
The means by which computer viruses spread can differ depending on the type of virus and the compromised device’s security settings. Many software is propagated via email messages, websites or various file formats. Email attachments serve as a vector for spreading computer viruses; they can either be attached directly to an email or embedded within its contents. Suppose an email attachment is infected with a virus. In that case, it can infect not only the device upon which it is opened but also any other devices onto which this infected attachment is copied. Furthermore computer viruses can also disseminate through websites that host software—, for instance social media platforms that distribute counterfeit videos, images or other deceptive content.
Websites can also contain code that can infect a device when a user clicks on a link or visits the site.
The symptoms of an infection depend heavily on the type of virus that has infected a device. General symptoms of an infection include the following:
- A computer that is running more slowly than normal
- A large amount of data being sent or received
- A computer that is excessively using its memory or processor
- A large number of pop-up advertisements
- A computer that runs programs automatically when it’s not in use
- A large amount of data being deleted from a computer
These symptoms could be an indication that a computer has been infected with the Trojan.Injector virus. If you’re experiencing any of these symptoms it’s advisable to scan your device for viruses. Utilizing a computer virus scanner can help in identifying viruses and other malicious software on your device. However it’s important to keep in mind that these scanners may not always be entirely accurate so its recommended to take steps to confirm the results. In case your computer is indeed infected with a computer virus you might want to take measures to clean your device.
Computer viruses can have impacts on both the computer and the users data. They can disrupt operations, damage data. Even render a computer unusable. Additionally certain computer viruses are capable of spreading to computers and networks leading to simultaneous infections, across multiple devices. These types of viruses can cause harm and prove challenging to remove. In some instances it may be necessary to purchase devices or restore data from a backup in order to completely eliminate the presence of the Trojan.Injector virus. Given the risks associated with computer viruses users should take precautions to safeguard their devices against infections.
Detecting the presence of the Trojan.Injector computer virus often proves challenging. It is recommended that users regularly check their devices for viruses since detecting an infection while it is occurring can be difficult.
To determine if your devices are infected with any viruses you can utilize antivirus software. Simply follow the instructions provided below.
How to remove Trojan.Injector
Malwarebytes anti-malware is an essential tool in the fight against malware. Malwarebytes can remove many types of Trojan.Injector malware that other software does often miss. Malwarebytes is costing you absolutely nothing. When cleaning up an infected computer, Malwarebytes has always been free, and I recommend it as an essential tool in the battle against malware.
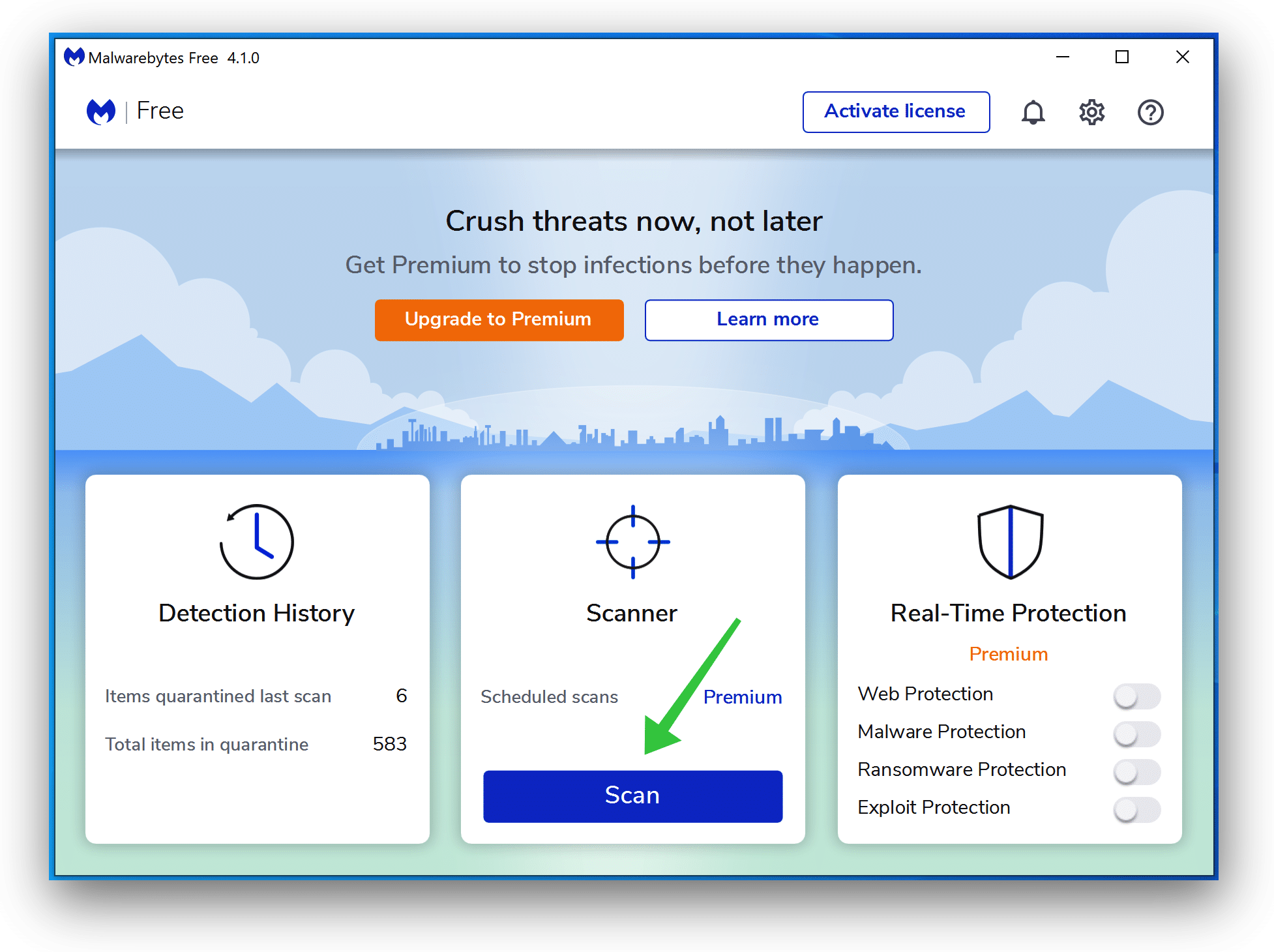
Install Malwarebytes, and follow the on-screen instructions.
Click Scan to start a malware scan.
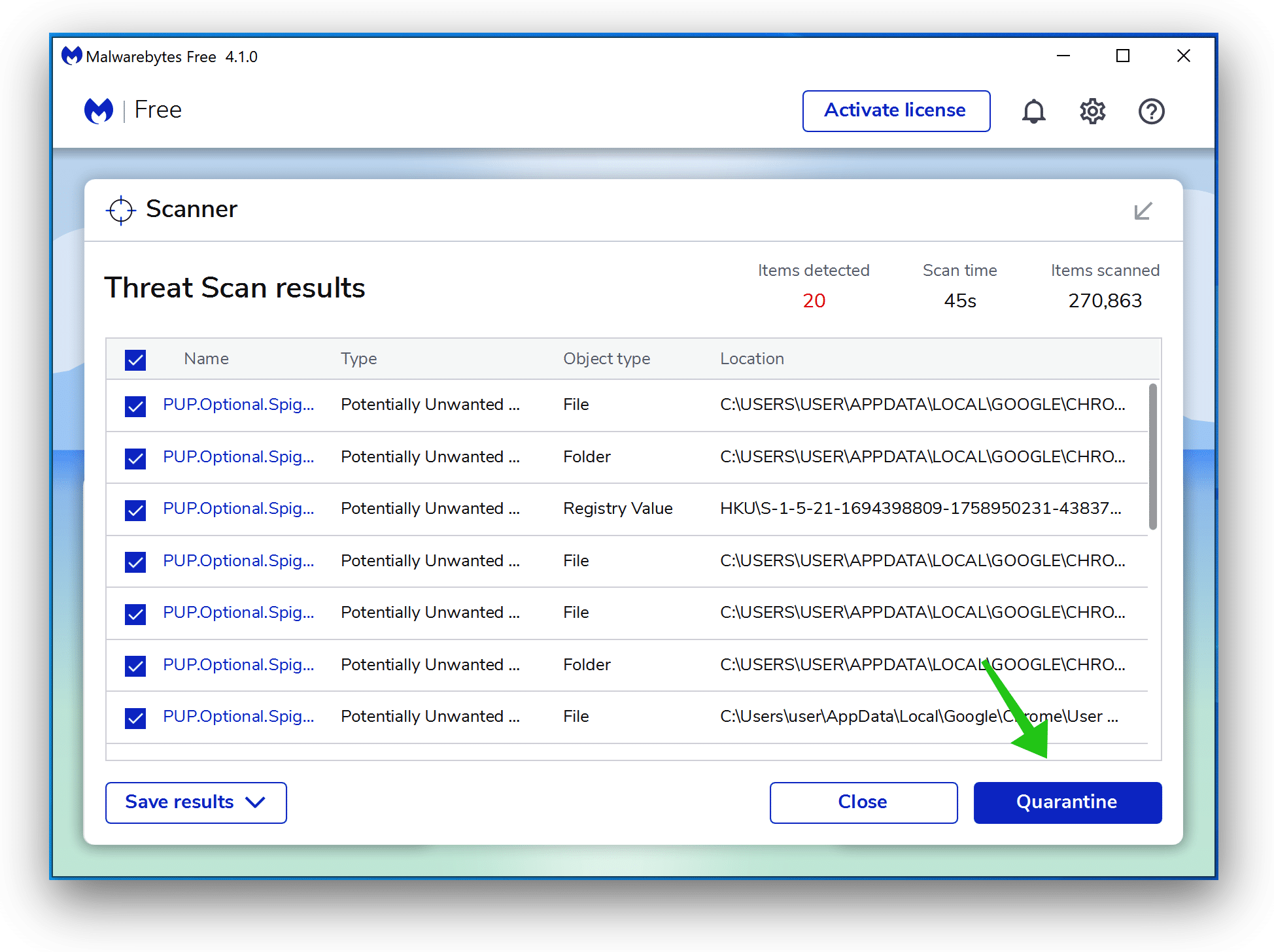
Wait for the Malwarebytes scan to finish. Once completed, review the Trojan.Injector adware detections.
Click Quarantine to continue.
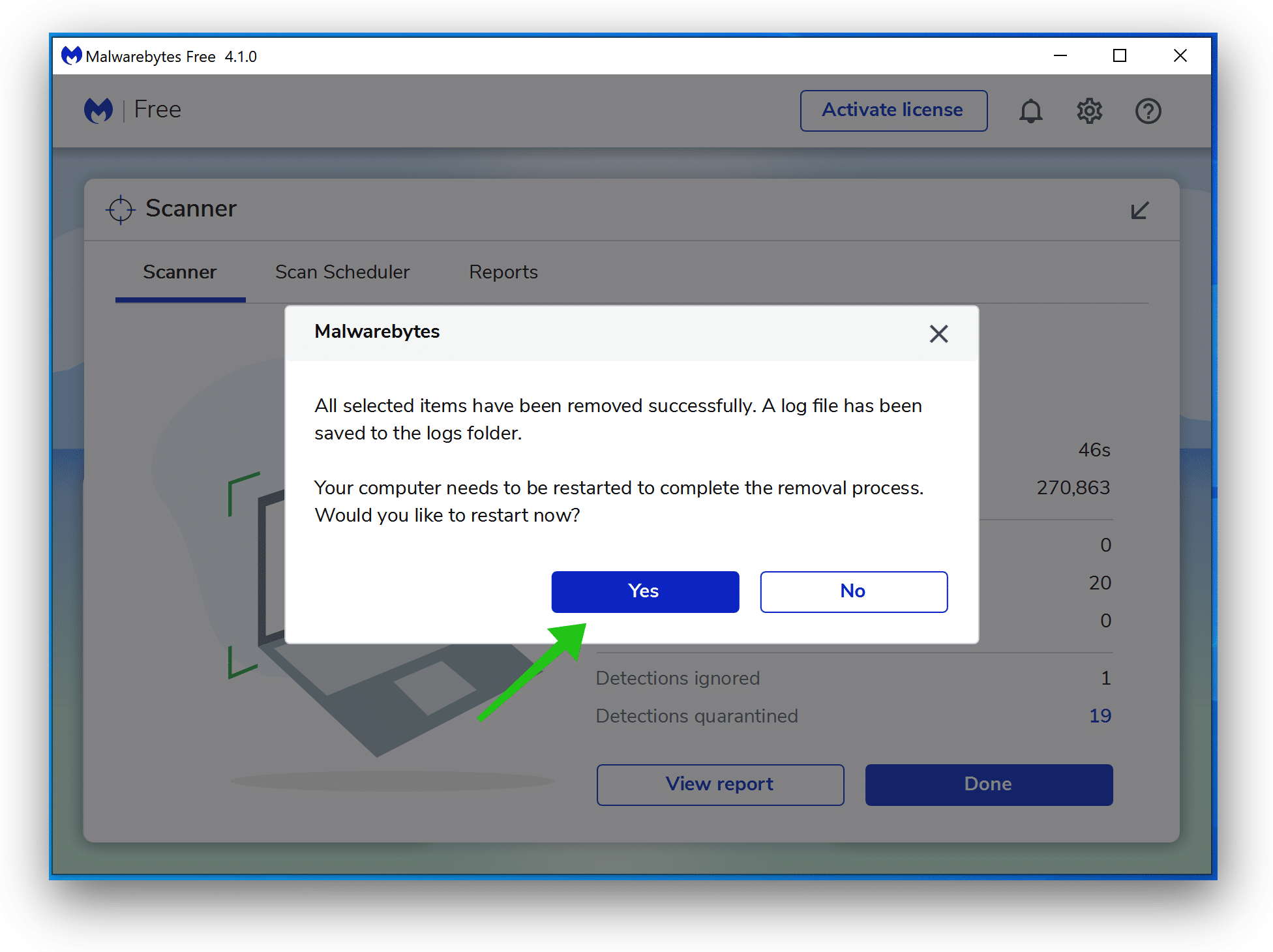
Reboot Windows after all the adware detections are moved to quarantine.
Continue to the next step.
Remove unwanted programs with Sophos HitmanPRO
In this second malware removal step, we will start a second scan to ensure no malware remnants are left on your computer. HitmanPRO is a cloud scanner that scans every active file for malicious activity on your computer and sends it to the Sophos cloud for detection. In the Sophos cloud, both Bitdefender antivirus and Kaspersky antivirus scan the file for malicious activities.
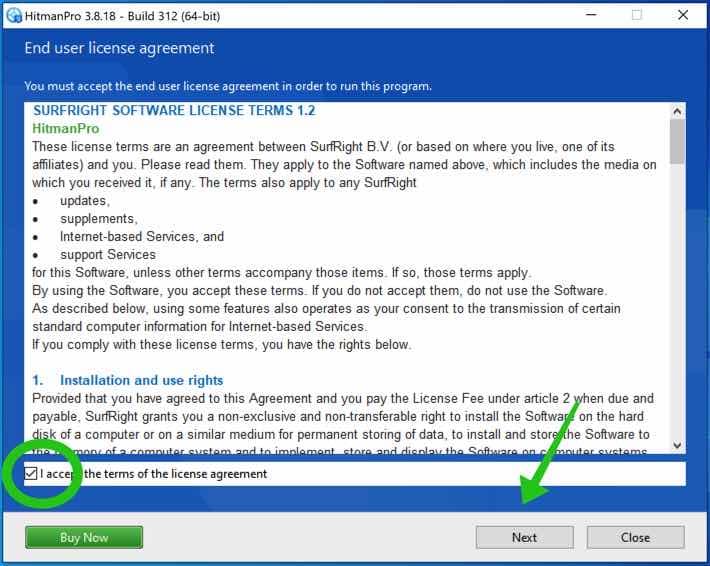
When you have downloaded HitmanPRO install the HitmanPro 32-bit or HitmanPRO x64. Downloads are saved to the Downloads folder on your computer.
Open HitmanPRO to start installation and scan.

Accept the Sophos HitmanPRO license agreement to continue. Read the license agreement, check the box, and click on Next.
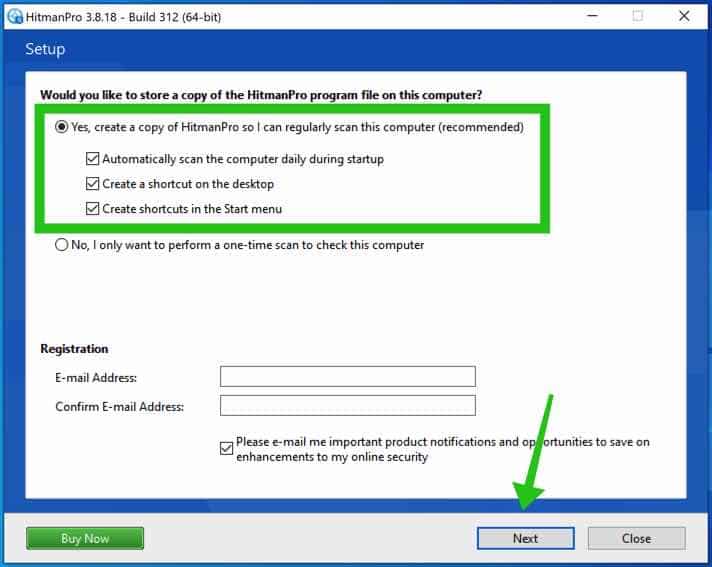
Click the Next button to continue Sophos HitmanPRO installation. Make sure to create a copy of HitmanPRO for regular scans.
HitmanPRO begins with a scan, wait for the antivirus scan results.
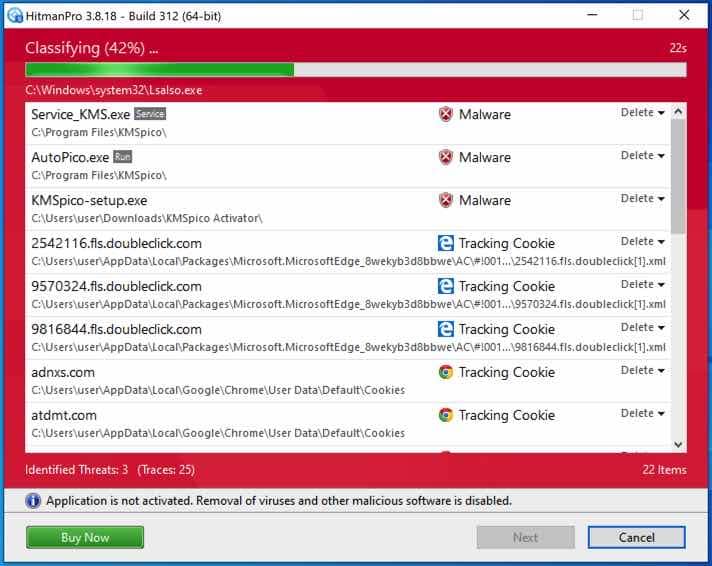
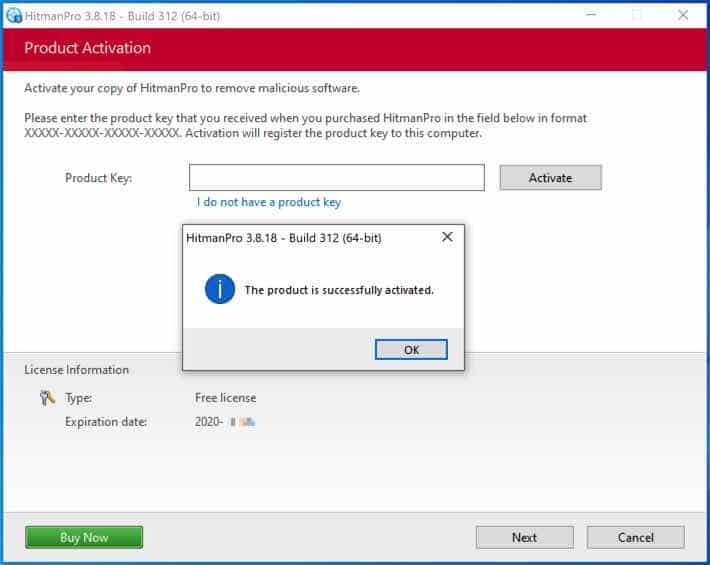
After the scan, click Next and activate the free HitmanPRO license. Click on Activate Free license.
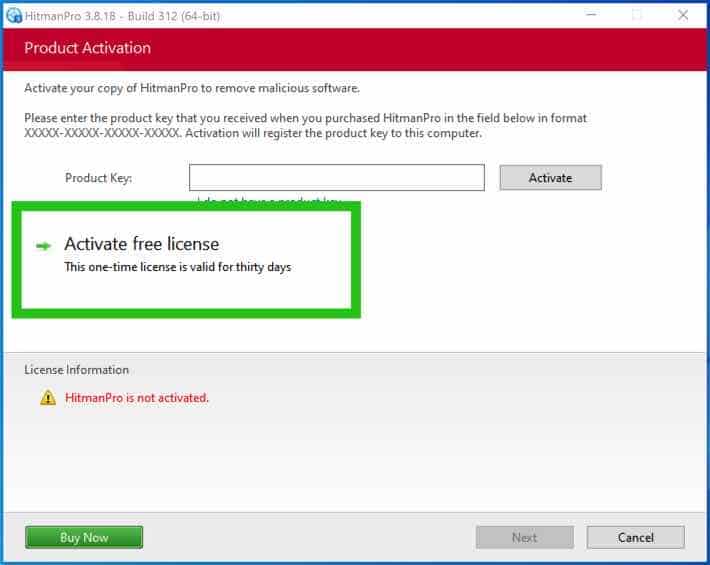
Enter your e-mail for a Sophos HitmanPRO free thirty days license. Click on Activate.
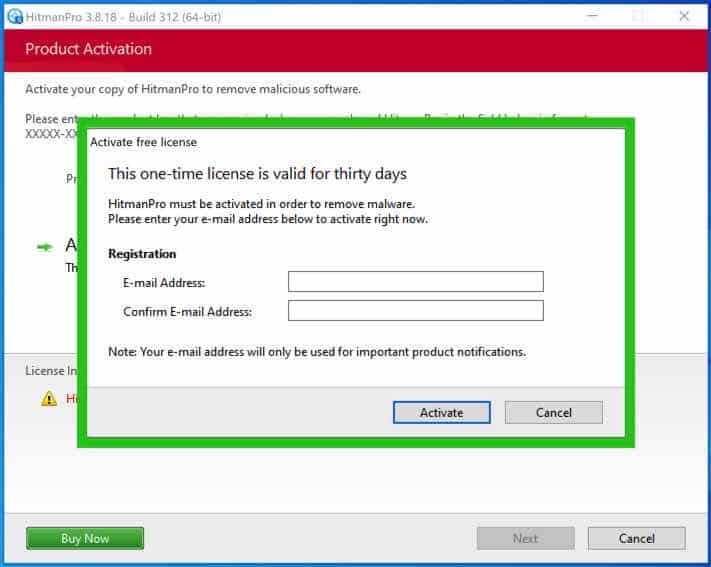
The free HitmanPRO license is successfully activated.
You’ll be presented with the malware removal results. Click Next to continue.
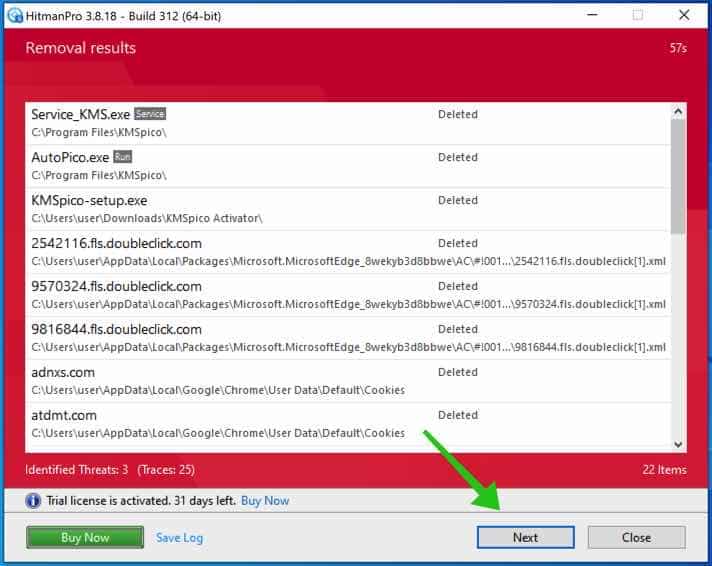
Malicious software was partially removed from your computer. Restart your computer to complete the removal.
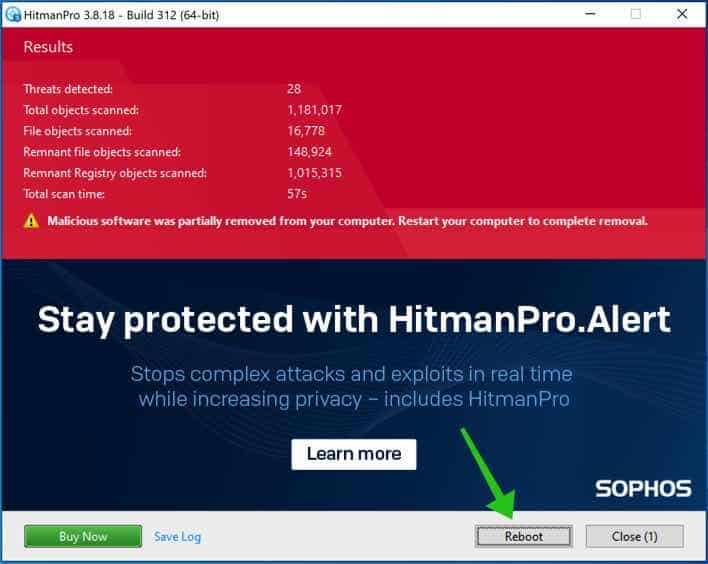
Bookmark this page when you reboot your computer.
How to prevent Trojan.Injector virus?
The effective measure to guard against the Trojan.Injector virus is to install antivirus software on all devices, like Malwarebytes. Additionally it’s crucial to update the software patches and security features of all devices connected to a network. It is advisable to refrain from clicking on links in emails from senders downloading files from unknown websites or visiting websites notorious for spreading viruses or malicious software.
Furthermore exercise caution when opening email attachments unless they are anticipated. Before opening any expected links or email attachments scan them using antivirus software. Be mindful of the devices you connect to your network and the removable media used for transferring data between devices. It’s important to note that no device can guarantee immunity against viruses. With antivirus software installed devices can still be susceptible, to computer viruses.
To safeguard against computer viruses follow these practices;
- Keep all devices up-to-date with the latest software updates.
- Use antivirus software on all devices.
- Scan all links, files, and email attachments before opening them.
- Avoid clicking on links from unknown senders.
- Avoid downloading files from unknown websites.
- Avoid visiting websites that are known to distribute viruses or malicious software.
- Be careful about what devices you plug into your network.
- Be careful about what removable media you use to transfer data between devices.
- Regularly check your devices for viruses.
I hope this helped. Thank you for reading!